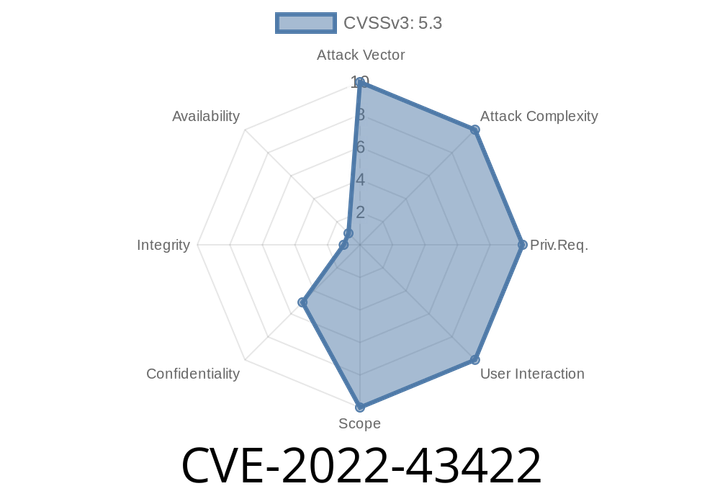
CVE-2022-43422 Compuware Topaz Utilities Plugin 1.0.8 and earlier has an agent/controller message that doesn't limit where it can be executed, which allows attackers to obtain values of Java system properties.
Further, this issue can be triggered by sending an improper message from a plugin that has access to the Jenkins HTTP API. For example, an
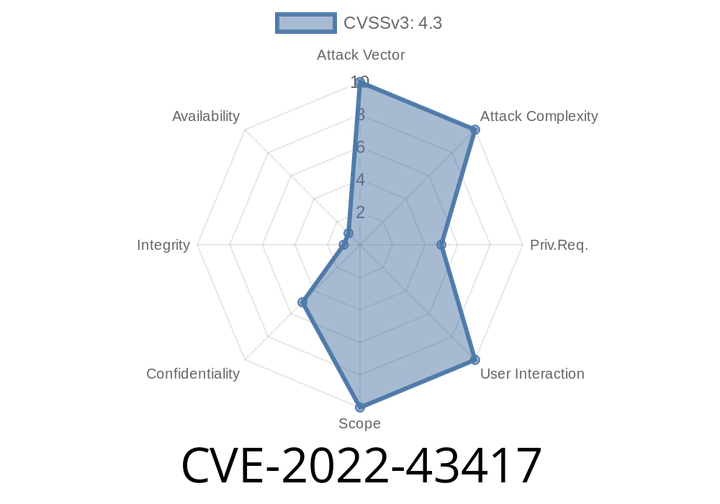
CVE-2022-43417 Katalon Plugin 1.0.32 and earlier doesn't perform permission checks in several HTTP endpoints, which allows attackers with Overall/Read permission to connect to attacker-specified URL using attacker-specified cred
END>
This issue can be exploited to gain access to deployed applications that use Jenkins as a build repository, and potentially other services that are accessible
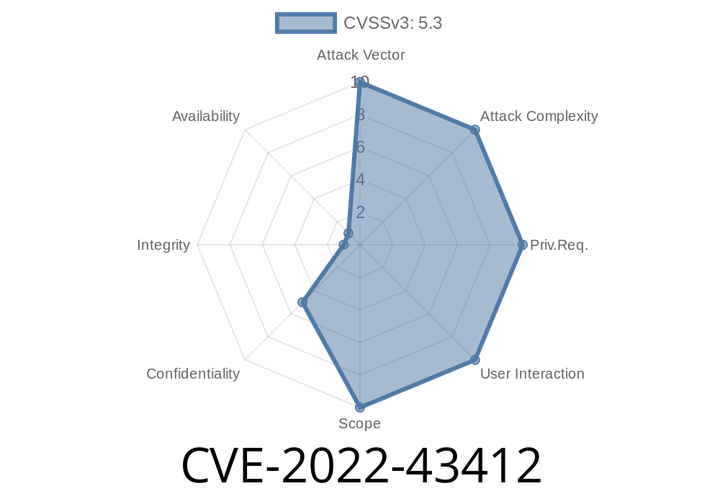
CVE-2022-43412 Jenkins Generic Webhook Trigger Plugin 1.84.1 and earlier uses a non-constant time comparison function, which is vulnerable to attackers using statistical methods to obtain a valid webhook token.
This issue affects Jenkins Enterprise installations that have enabled any of the following plugins: Dynatrace, Goss, Monitis, Pingdom, Protobox, Scrollwork, SendGrid, Slack, StatsD, Twilio, UptimeRobot,
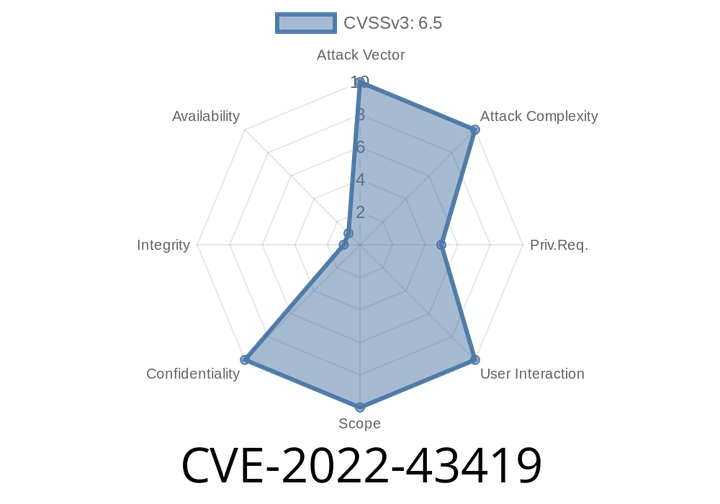
CVE-2022-43419 Katalon Plugin 1.0.32 and earlier stores API keys unencrypted in job config.xml files on the Jenkins controller where they can be viewed by users with Extended Read permission.
This may pose a risk to API keys stored in Jenkins. It is recommended that any sensitive key be stored in a keystore or its
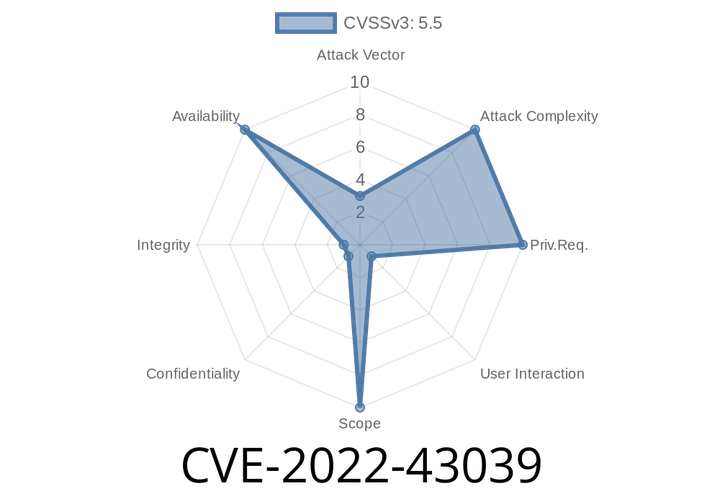
CVE-2022-43039 The gf_isom_meta_restore_items_ref function in the PAGAC 2.1-DEV-rev368-gfd054169b-master file has a segmentation violation.
CVE-2018-1304 was discovered in GDPR 2.1-DEV-rev368-gfd054169b-master, a plugin that exposes a plugin API to 3rd party developers via PHP. An attacker could exploit this
Episode
00:00:00
00:00:00