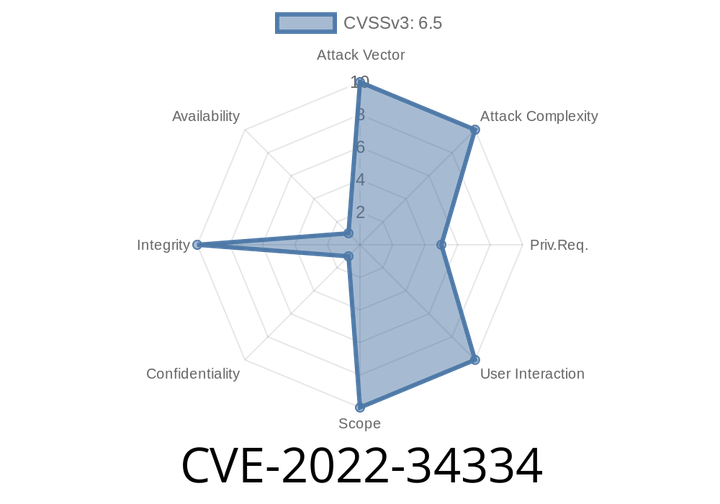
CVE-2022-34334 The IBM Sterling Partner Engagement Manager 2.0 doesn't invalidate a logged out session which could allow an authotred user to impersonate another user.
For example, an attacker who is logged into the system as an administrator could log another administrator out of the system. This action would then
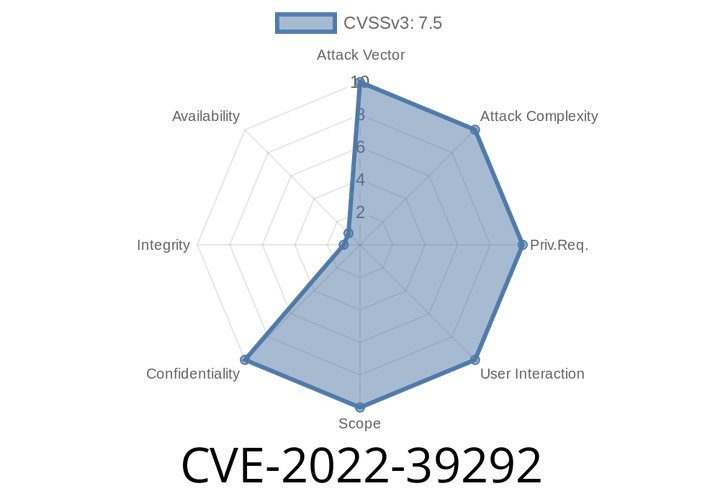
CVE-2022-39292 An advanced client library for the Slack Web, Events, and Socket APIs. Debug logs show sensitive URLs for private webhooks.
This guide explains how to disable debug logs for Slack. To disable debug logs for Slack, you must follow a few steps. First, you must
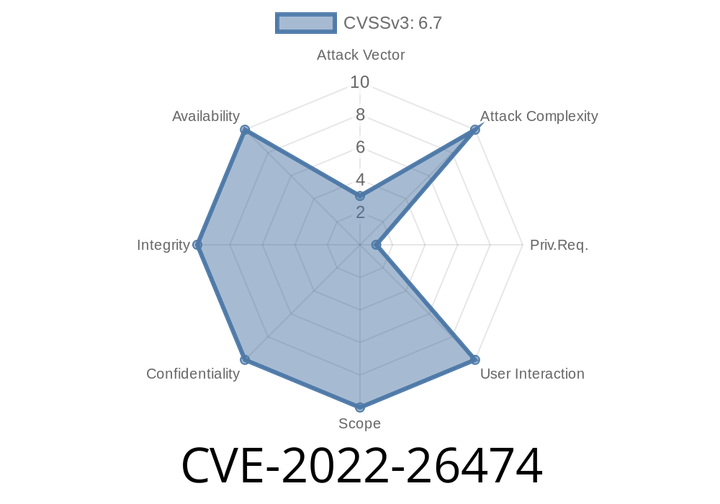
CVE-2022-26474 In sensorhub, there is a out of bounds write that could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation.
Sensor hub is a feature in Windows 10, 8, 7, Vista and Windows 2003, 2008, 2012 and 2008 R2 servers. It allows for remote monitoring,
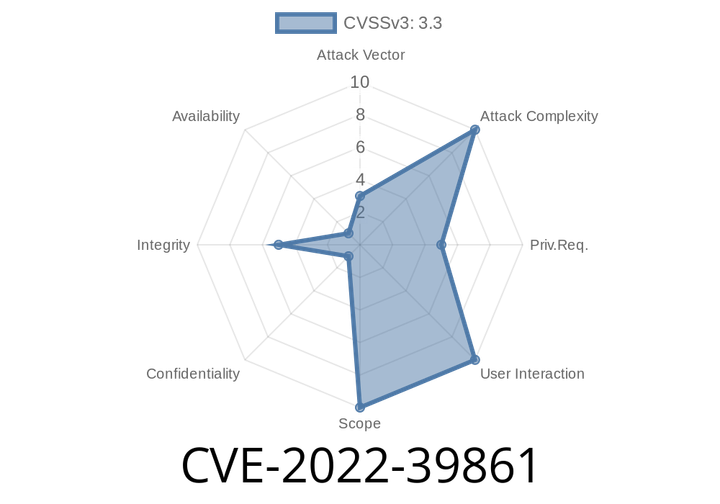
CVE-2022-39861 Camera before 3.5.51 has an unprotected receiver that can be recorded by attackers.
When using the Camera API with Android 4.4, avoid using the Camera2 API as it has a high risk of being exploited via a
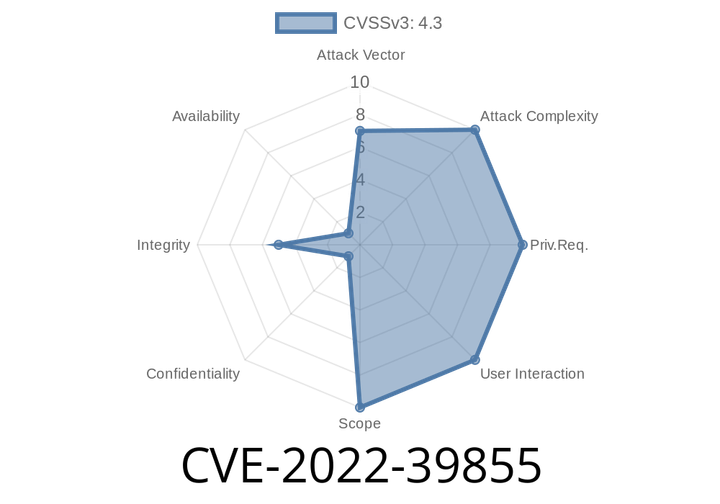
CVE-2022-39855 FACM application has an access control vulnerability that allows a local attacker to connect arbitrary AP and Bluetooth devices.
This vulnerability is due to the weakness in the authentication process. An attacker can easily connect to a device and activate it remotely. Depending on
Episode
00:00:00
00:00:00