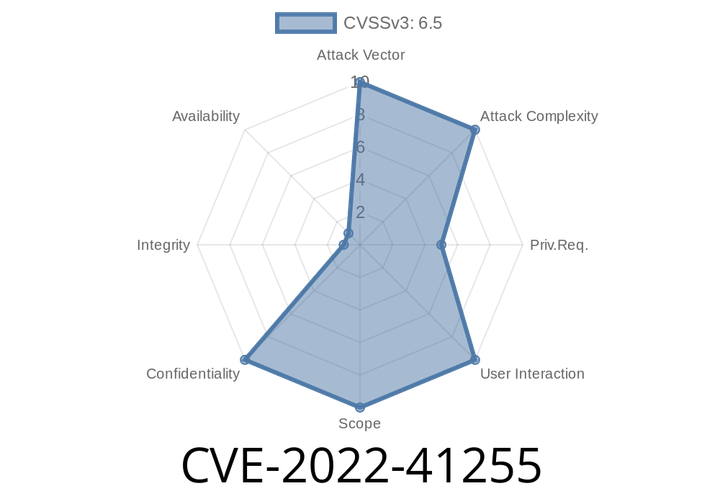
CVE-2022-41255 The Cons3rt API token was stored unencrypted in job config.xml files on the Jenkins controller where it could be viewed by users with access to the Jenkins controller file system.
This may result in malicious actors gaining access to the API token used to authenticate with the Cons3rt service, potentially giving them the ability to
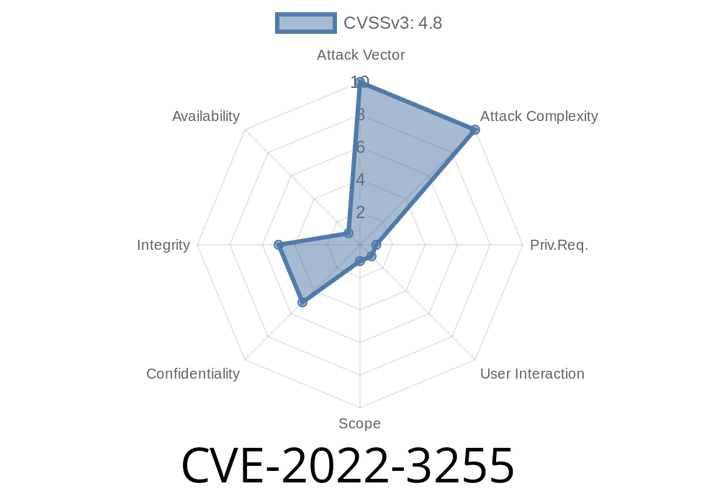
CVE-2022-3255 An attacker can control a user's browser and perform actions within the application.
The attacker does not have to be fully aware of the application's internal workings to leverage these mechanisms. For example, an attacker could
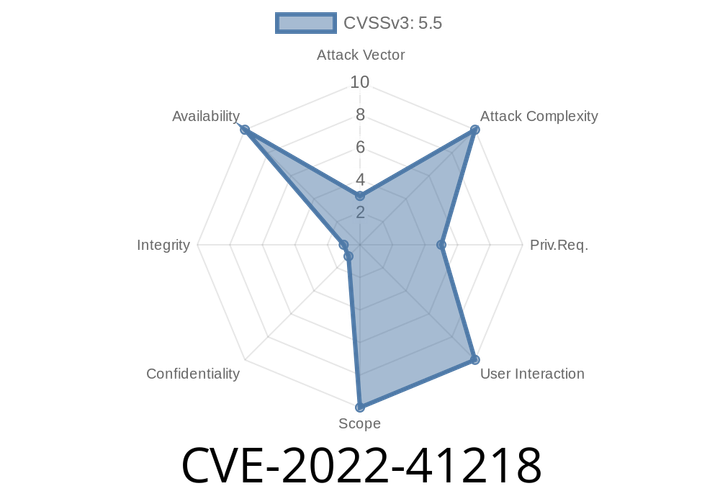
CVE-2022-41218 Driver uses refcount races to affect dvb_demux_open and dvb_dmxdev_release.
Due to limitation in the API, when doing a dvb_demux_close(device) followed by a dvb_device_get(device) from the same device, the
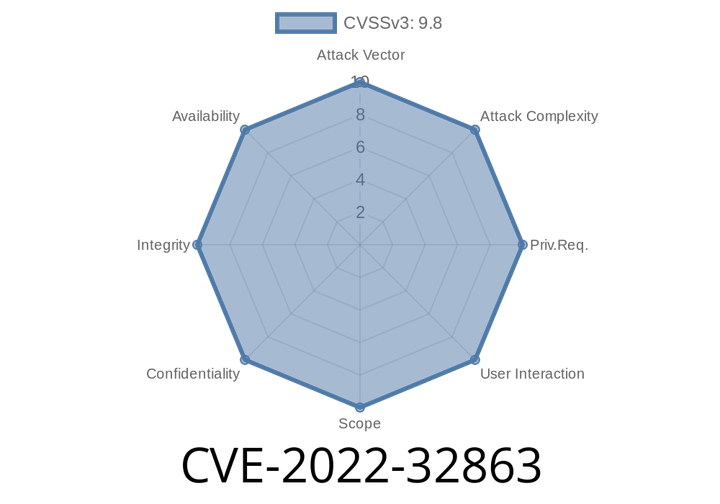
CVE-2022-32863 Memory corruption issue fixed in Safari 15.6, macOS Monterey 12.5.
This issue is fixed in Safari 15.5, macOS High Sierra 10.13.1. It may be possible to use social engineering techniques to trick
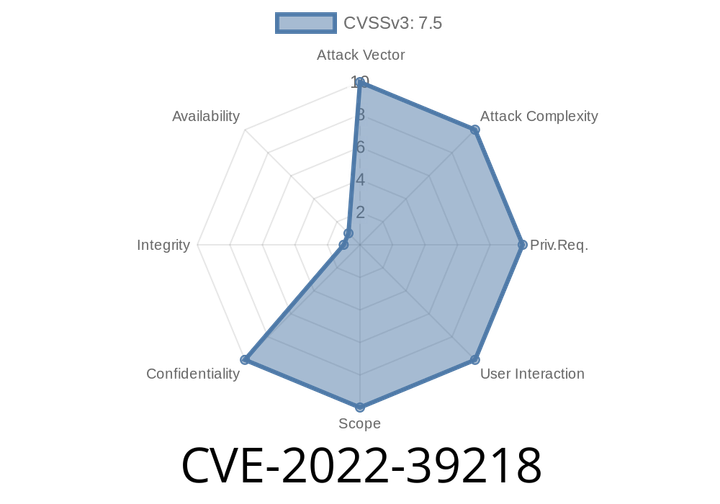
CVE-2022-39218 The JS Compute Runtime for Compute@Edge is the environment JavaScript is executed in when using the Compute@Edge JavaScript SDK.
When using the `crypto.getRandomValues` method on a `Compute@Edge` instance, a small bug in the JS Compute Runtime that was previously unpatched allows the
Episode
00:00:00
00:00:00