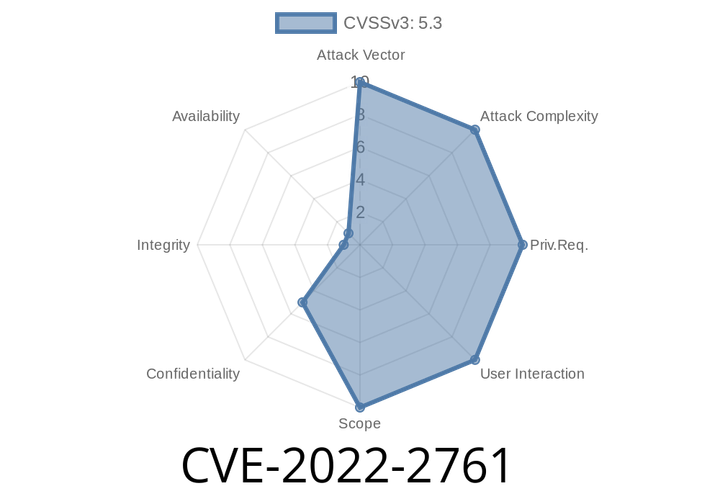
CVE-2022-2761 - How an Information Disclosure Bug in GitLab Leaked Restricted Resource Names via Jira Issues
In mid-2022, a vulnerability was uncovered in GitLab Community Edition (CE) and Enterprise Edition (EE), identified as CVE-2022-2761. This bug let attackers discover the names
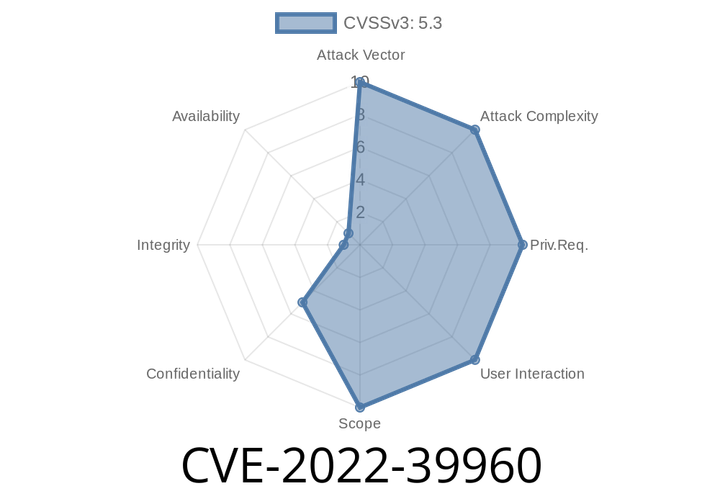
CVE-2022-39960 The Netic Group Export add-on before 1.0.3 for Atlassian Jira does not perform authorization checks
An attacker with control over a victim’s Jira instance could use this flaw to export all groups from the Jira instance to a remote
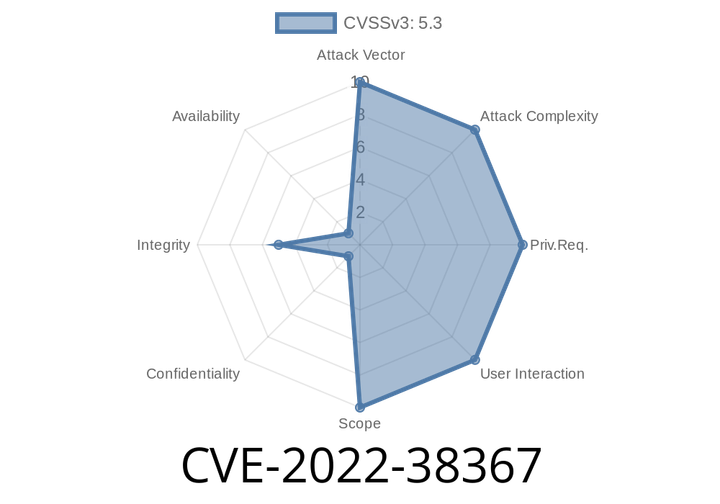
CVE-2022-38367 The Netic User Export add-on before 2.0.6 for Atlassian Jira does not perform authorization checks
This issue has been fixed in Jira 7.0.6 and later. Additionally, the LDAP Authenticated Users permission gives full control over the LDAP server
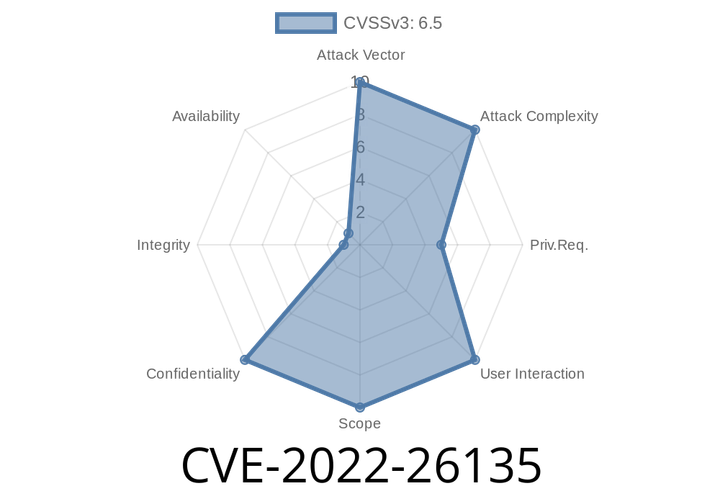
CVE-2022-26135 The Mobile Plugin for Jira Data Center and Server has an endpoint that can be brute-forced by a remote, authenticated user.
The vulnerability can be exploited if the user has permissions to access the ‘batch’ feature on the target server. We recommend not relying on this
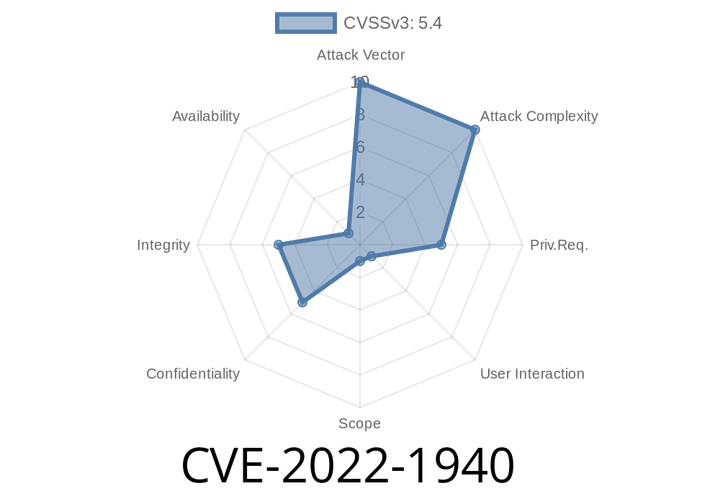
CVE-2022-1940 Jira integration in GitLab EE is vulnerable to stored cross-site scripting, and is affected by versions 13.11-14.9.5, 14.10-14.10.4, and 15.0-15.0.1
The proof of concept (PoC) code is as follows: function doit() { var target = ‘URL of GitLab EE>'; alert(‘You clicked on “‘ + target + ’”!’); } When
Episode
00:00:00
00:00:00