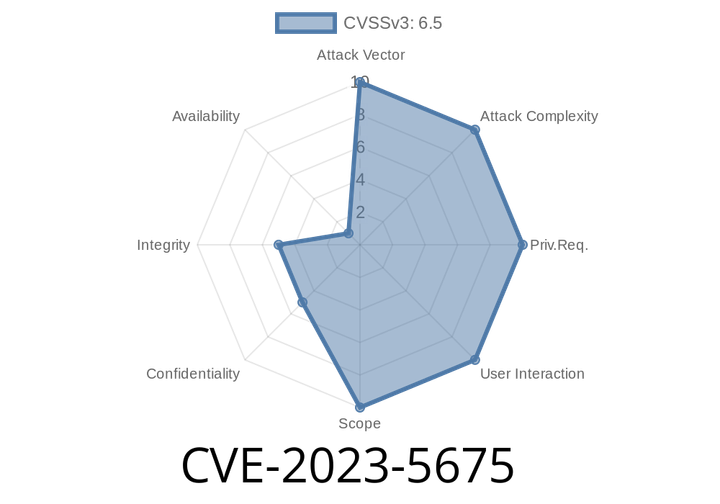
CVE-2023-5675 - Quarkus Authorization Bypass via Abstract Classes and Extensions – Exploit Explained
Summary:
CVE-2023-5675 is a significant security vulnerability that affects Java applications using Quarkus, specifically those using the RestEasy Classic or Reactive JAX-RS endpoints. If your
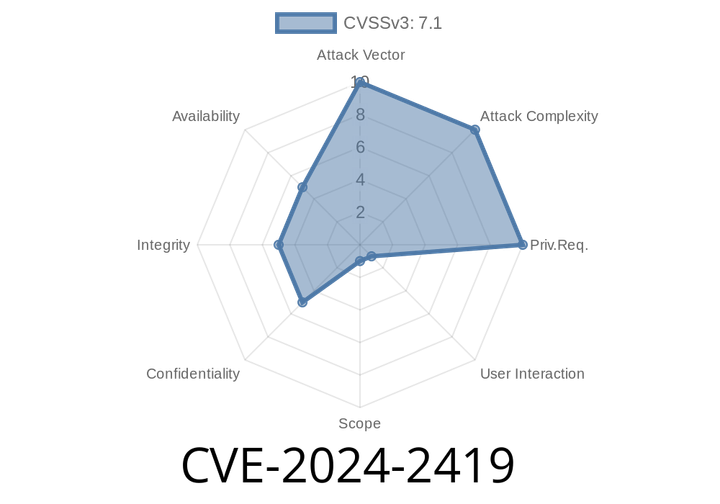
CVE-2024-2419 - Keycloak’s Redirect_URI Bypass, Token Theft Made Easy
Keycloak is a pretty popular open-source identity and access management tool, commonly used to handle login and single sign-on (SSO) for web applications. Security is
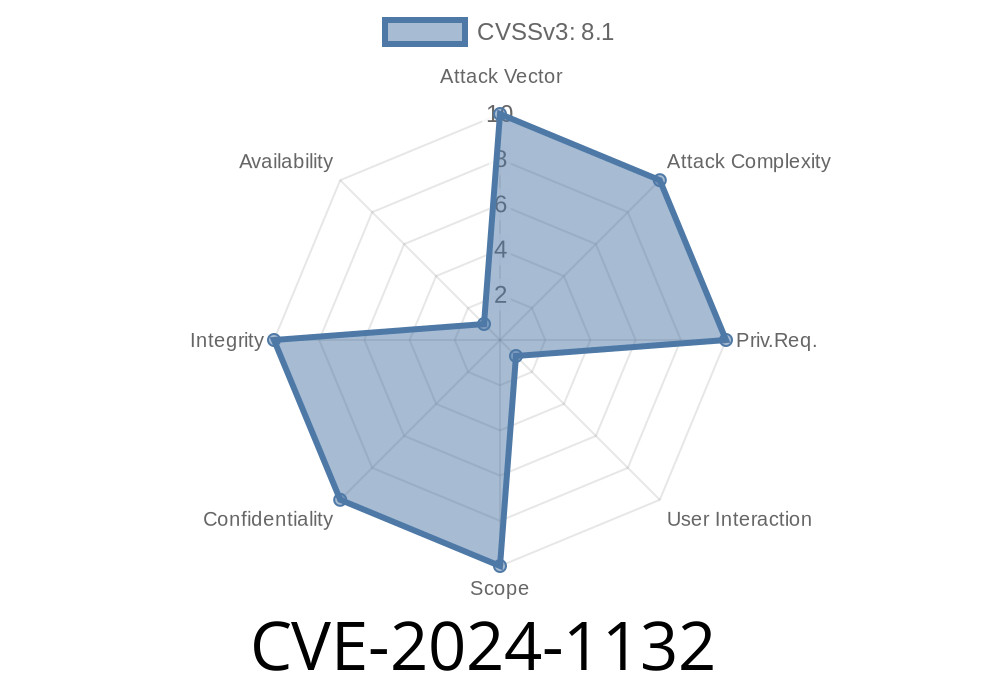
CVE-2024-1132 - Keycloak Unsecured Redirect Vulnerability Exposed
---
Overview
A critical flaw, tracked as CVE-2024-1132, was discovered in Keycloak—an open-source identity and access management solution. This vulnerability is related to improper
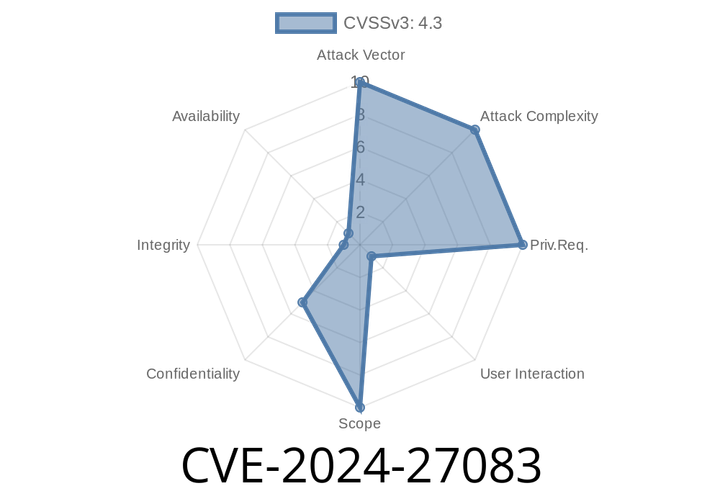
CVE-2024-27083 - Critical XSS Vulnerability in Flask-AppBuilder OAuth Login Page Explained
Flask-AppBuilder (FAB) is a popular application development framework built on top of Flask, and it’s widely used in projects for building web apps with
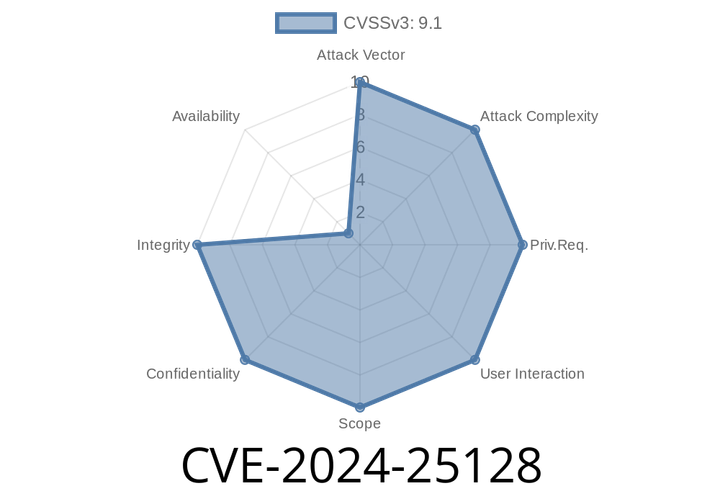
CVE-2024-25128 - Exploiting Flask-AppBuilder OpenID Vulnerability – What You Need To Know
Flask-AppBuilder (FAB) is one of the most popular frameworks built on top of Flask, used for quickly spinning up powerful web applications with rich authentication
Episode
00:00:00
00:00:00