CVE-2022-45141 - Windows Kerberos RC4-HMAC Elevation of Privilege Vulnerability, Explained for Real-World Admins
On November 8, 2022, Microsoft publicly disclosed a critical security vulnerability (CVE-2022-45141) affecting the RC4-HMAC encryption type in Kerberos authentication. This vulnerability doesn't
CVE-2023-20052 - How a Flaw in ClamAV’s DMG DMG Parser Led to Information Disclosure
On February 15, 2023, a serious security vulnerability was published in ClamAV, the popular open-source antivirus engine. Unauthenticated attackers could exploit it remotely, leaking sensitive
CVE-2023-1017 - Exploiting Out-Of-Bounds Write in TPM2. for Denial of Service and Code Execution
Trusted Platform Module (TPM) is a critical security chip you’ll find in countless devices, from laptops to enterprise servers. TPM2. is the latest mainstream
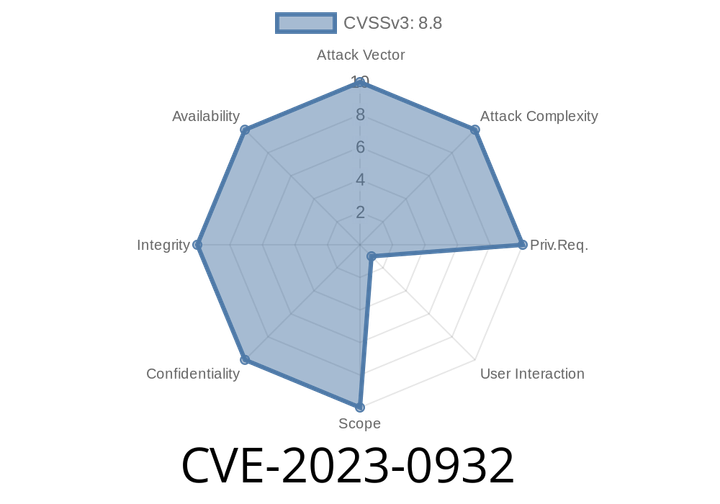
CVE-2023-0932 - Exploiting a "Use-After-Free" in Chrome WebRTC (Simple Terms with Exploit Walkthrough)
CVE-2023-0932 is a serious bug found in Google Chrome’s WebRTC component. WebRTC lets you make video calls, voice calls, and share files—all inside
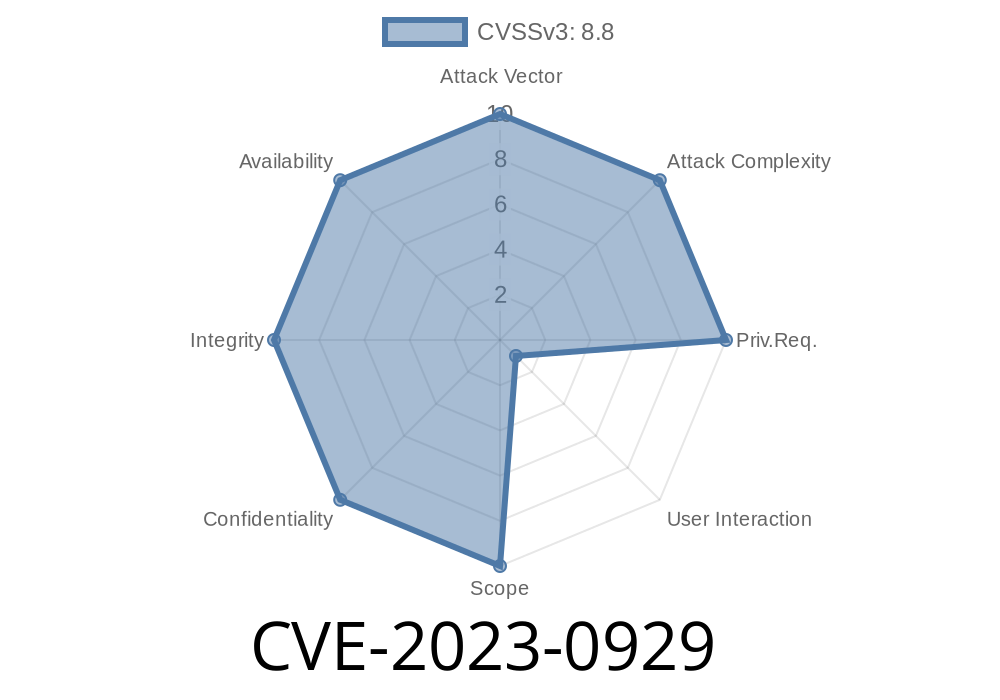
CVE-2023-0929 - Understanding the Use-After-Free in Vulkan (Google Chrome) And How Attackers Can Steal Control
---
*In early 2023, security researchers discovered a severe vulnerability in Google Chrome’s handling of the Vulkan graphics API. Marked as CVE-2023-0929, this flaw
Episode
00:00:00
00:00:00