CVE-2021-27862 Filtering on the Layer 2 network can be bypassed using invalid LLC/SNAP headers and Ethernet to Wifi frame conversion.
These types of bypasses are possible if the device that is being targeted is running an operating system that supports these Layer 2 technologies. Operating
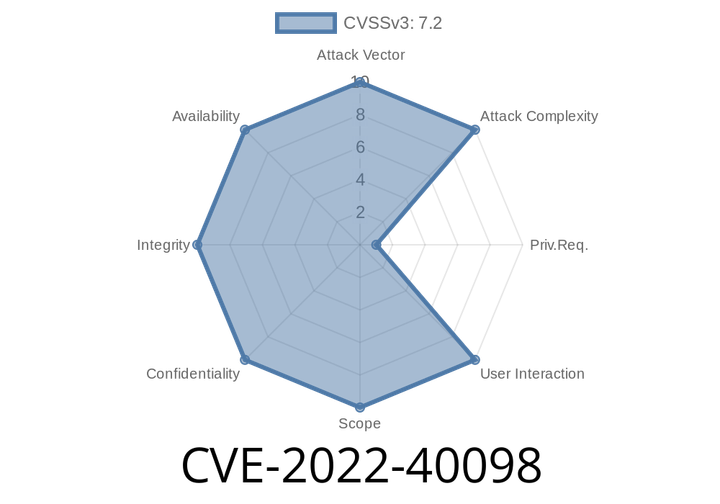
CVE-2022-40098 The ID of the expense update system was found to be vulnerable to a SQL injection attack.
If exploited, this would allow an attacker to execute arbitrary SQL commands against the application.
On July 14th 2018, it was discovered that The official
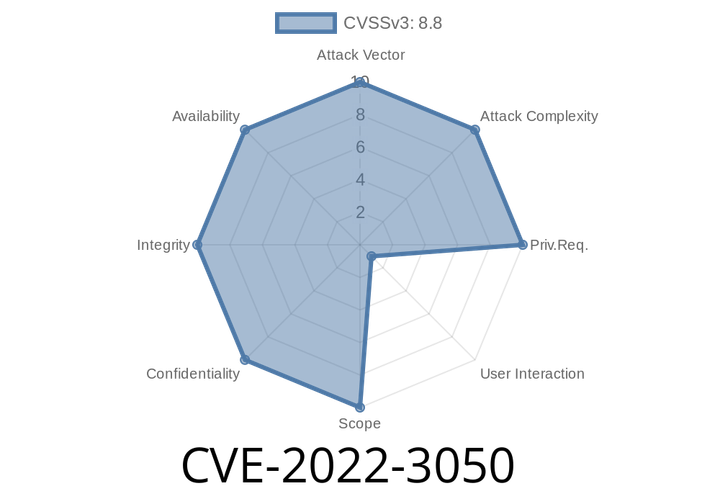
CVE-2022-3050 Heap buffer overflow in WebUI in Chrome on Chrome OS prior to 105.0.5195.52 allowed a remote attacker who convinced a user to engage in specific UI interactions to exploit heap corruption.
CVE-2018-5602 has been assigned to this issue. Google confirmed this vulnerability was limited to privileged users who had full control of the browser, rather than
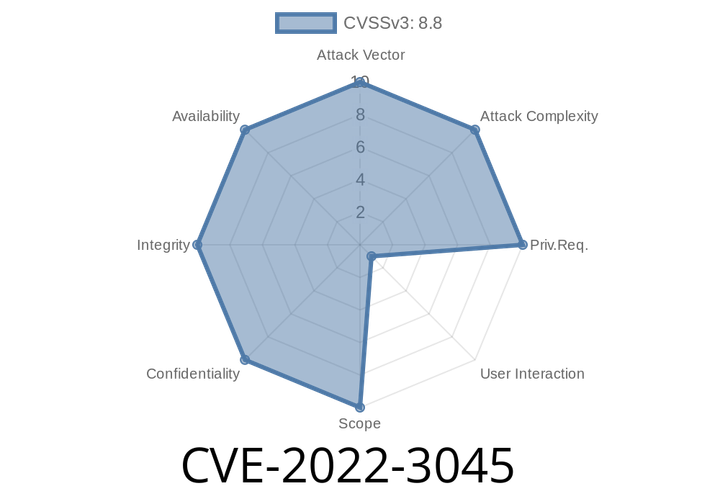
CVE-2022-3045 V8's validation of untrusted input was insufficient in Google Chrome prior to 105.0.5195.52. This could lead to heap corruption.
CVE-2018-6063: A remote code execution vulnerability in Blink/Webkit components was fixed in V8 in Google Chrome OS prior to 69.0.3497.81. The
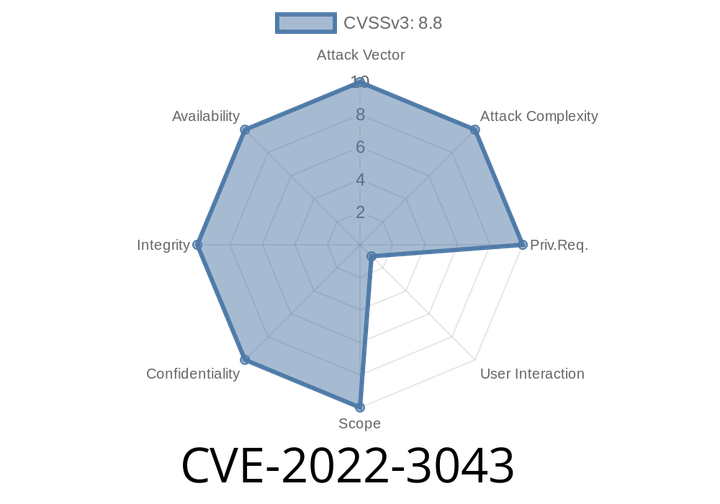
CVE-2022-3043 Heap buffer overflow in Screen Capture in Google Chrome on Chrome OS prior to 105.0.5195.52 allowed a remote attacker to exploit heap corruption if they convinced a user to engage in specific UI interactions.
It was reported that this issue did not occur in the staging environment due to changes implemented since the last release. A user had to
Episode
00:00:00
00:00:00