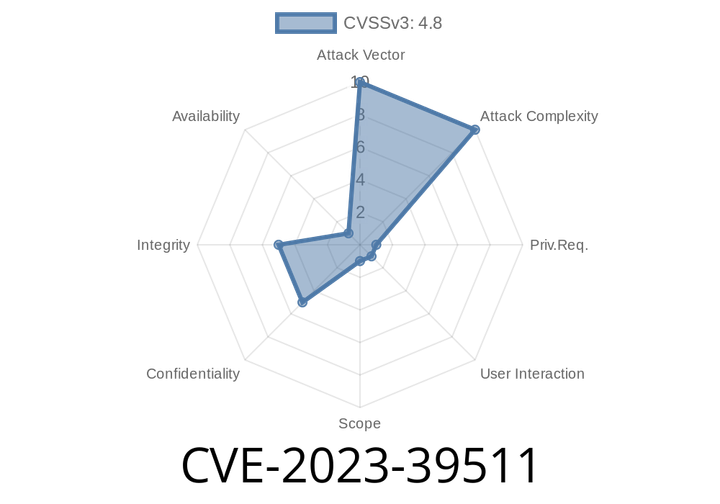
CVE-2023-39511 - How a Simple Device Name Can Compromise Cacti Admins (Exploit & Remediation Guide)
Cacti is a popular open source platform used by IT teams for monitoring networks and devices. In July 2023, a significant security flaw was discovered:
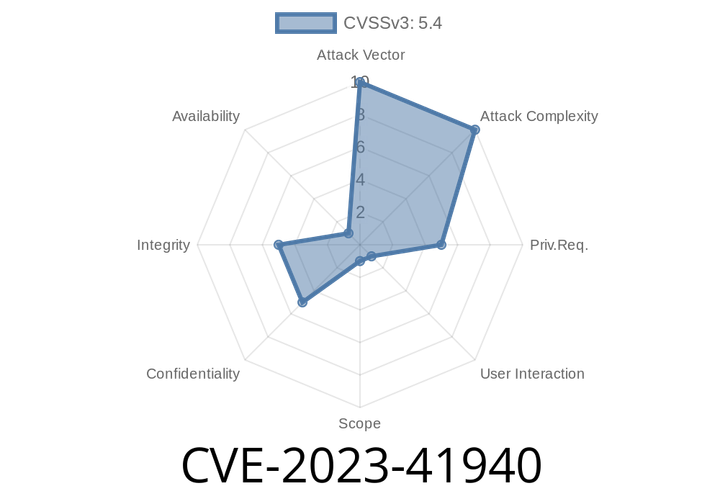
CVE-2023-41940 - Exploiting Stored XSS in Jenkins TAP Plugin (Advisory, Exploit, and Mitigation Guide)
Jenkins is a widely used open-source automation server, critical for building and deploying many projects worldwide. However, plugins can sometimes introduce security holes if not
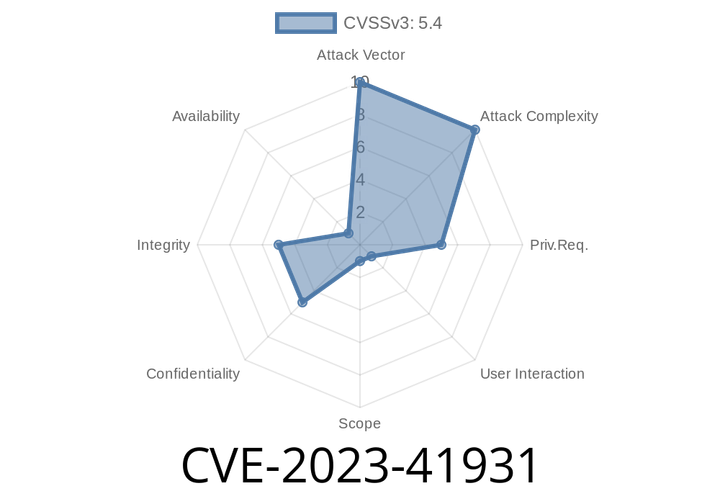
CVE-2023-41931 - Exploiting Jenkins Job Configuration History Plugin XSS Vulnerability (Detailed Walkthrough)
Jenkins is one of the most widely used open-source automation servers for continuous integration and continuous delivery (CI/CD). Plugins expand Jenkins features but sometimes
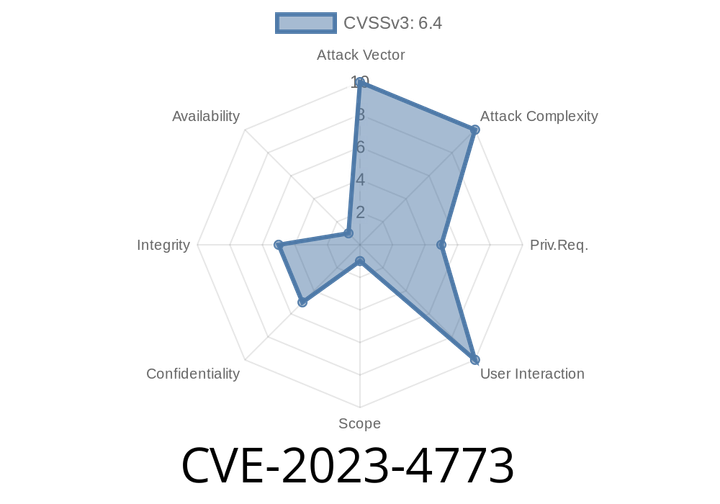
CVE-2023-4773 - Exploiting Stored XSS in WordPress Social Login Plugin (<= 3..4)
CVE-2023-4773 is a serious security vulnerability found in the popular WordPress plugin, Social Login, affecting versions up to 3..4. This bug allows attackers with
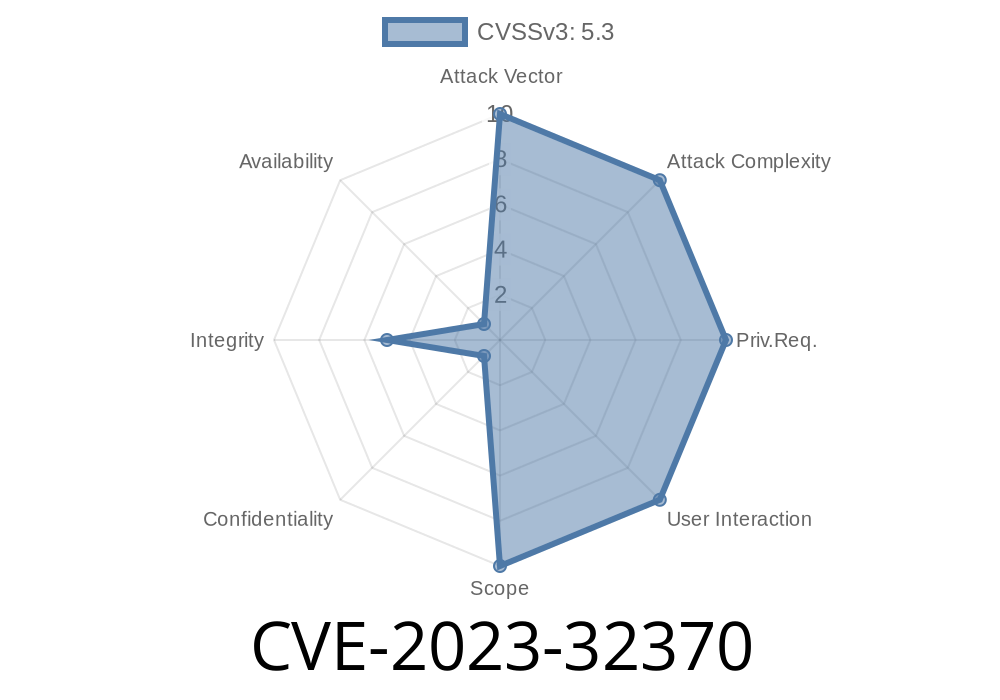
CVE-2023-32370 - How a Logic Flaw in macOS Ventura’s Content Security Policy Opened the Door to Wildcard Domain Bypass
In March 2023, Apple quietly patched a surprising security flaw in macOS Ventura 13.3—one that had the potential to let unwanted scripts or
Episode
00:00:00
00:00:00