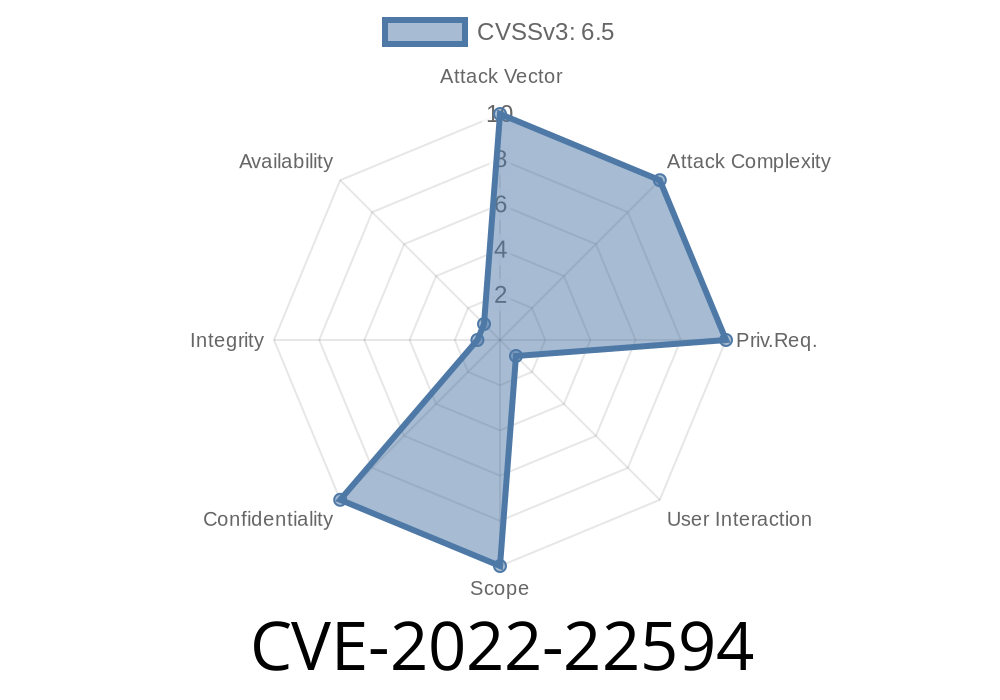
In January 2022, Apple patched a major privacy vulnerability: CVE-2022-22594. This bug exposed how IndexedDB—the main browser database for websites—could cross the boundaries between different sites (“origins”) in Apple’s WebKit engine. In practical terms: a malicious website could spy on sensitive data in your browser, including which other websites you’re logged into.
Below, I’ll walk you through what happened, why it mattered, how the exploit worked (with code!), and show you where it’s been explained in detail by security researchers.
What Is IndexedDB?
IndexedDB is a simple way for websites to store and retrieve data on your device. Each website is supposed to have *its own* database, and those databases should not be accessible to other sites due to the same-origin policy. If that rule is broken, it’s a serious problem.
CVE-2022-22594 — The Issue in Plain English
Apple’s WebKit implementation leaked the names of IndexedDB databases to all frames/tabs running in the browser—even if those frames belonged to a different site. So, if you had Gmail open in one tab, and a shady site in another, the shady site could check for the presence and names of Gmail’s databases. Many websites name their databases after user IDs or use predictable titles that can reveal user identity or at least website activity.
Security Implication:
A website you visit could snoop on what other sites you are visiting, whether you are logged in, and sometimes, who you are.
tvOS < 15.3
*The flaw was present throughout the Apple ecosystem, as all their browsers must use WebKit.*
How Did the Exploit Work?
Let’s see how an attacker could detect your activity.
1. Enumerating Database Names
IndexedDB exposes a webkit-specific method called indexedDB.databases(). In the buggy WebKit version, this method showed database names from ALL open tabs—no matter the origin.
JavaScript Example
if ('databases' in indexedDB) {
indexedDB.databases().then(dbs => {
dbs.forEach(db => {
console.log("Database name found:", db.name);
// Attacker could match these names to known database names from popular sites
});
});
}
A malicious website would periodically call this code and compare the database names it finds to a list of expected names for well-known services like Gmail, YouTube, Facebook, LinkedIn, etc.
2. Matching User Identity
Some web apps create per-user database names. For example, Google might name a database with your unique user ID. If a malicious site knows the pattern, it can scrape that value, fingerprint your Google account, and link your browsing activity to the real you—even if you’re in "private mode."
3. Real-World Impact
This bug was especially scary on iOS, where all browsers use Safari’s WebKit engine due to Apple’s App Store policies. Every browser was vulnerable—not just Safari.
What Did Apple Do?
The root of the bug was poor input validation and access control in IndexedDB’s implementation. Apple patched it by restricting access:
Cross-origin database enumeration is blocked.
Patched in:
References
- Apple’s Security Update Notes
- WebKit Security Advisory
- Detailed Research, FingerprintJS Blog
Proof-of-Concept (PoC) Code
This simple code, run on a *malicious site*, would leak database names from every open origin.
// Only works in vulnerable Safari/WebKit
indexedDB.databases().then(dbs => {
for (let db of dbs) {
// Log out each leaked database: name and origin
console.log("Leaked DB", db.name, db.origin);
// Here, attacker could exfiltrate db.name to a server
}
});
Example: If you’re logged into Gmail and its IndexedDB is named "https://mail.google.com:clientDb_12345", the attacker would see this name and know you are logged in.
How To Protect Yourself
- Update as soon as possible: Make sure your device (iPhone, iPad, Mac, Watch, TV) is running the latest software.
- Be cautious with suspicious links: Don't open untrusted websites while signed into sensitive services.
Conclusion
CVE-2022-22594 is a textbook example of why the same-origin policy matters. With a simple bit of JavaScript, malicious websites could spy on your browsing habits and possibly even your accounts. Thanks to quick disclosure and a timely patch from Apple, most users are now safe—if they update.
For more technical background:
- Official Apple Security Advisory
- Detailed Explanation by FingerprintJS (with live proof-of-concept demo)
Timeline
Published on: 03/18/2022 18:15:00 UTC
Last modified on: 03/28/2022 16:40:00 UTC