This could potentially allow an attacker to disable arbitrary plugins, leading to a plugin breakage and Site deactivation. We are actively investigating this issue, and have released a patch that adds the WordPress Verification API, which has authorisation and CSRF checks. We’d like to thank the security researchers at WordFence, who discovered this issue and reported it to us in our public security issue tracker. Verification of the Wordpress site is now enabled by default, and we strongly recommend that all users enable it too. If you are running a version of the Webmaster Tools Verification plugin prior to 1.2, we strongly recommend updating as soon as possible. Disabling plugin via Webmaster Tools is a very common task that almost all site owners perform, so it’s important that you consider this issue when updating to 1.2.
Plugin load order verification
The following is a list of recommended plugins, in order of preference, for verification.
WP-Exploit Scanner: This plugin makes it possible to scan your sites for exploitable vulnerabilities.
WP-Security Audit Log: This plugin makes it easy to track changes made to the site, so that you can see what changes have been made and who made them.
WordPress Security Tools: This plugin provides advanced security tools that are built specifically for WordPress websites.
Site Lockdown: This plugin blocks unwanted visitors from accessing the site on specific IP addresses or web browsers.
WordPress Website Security Scanner: This plugin scans your website for common vulnerabilities like SQL injection and XSS.
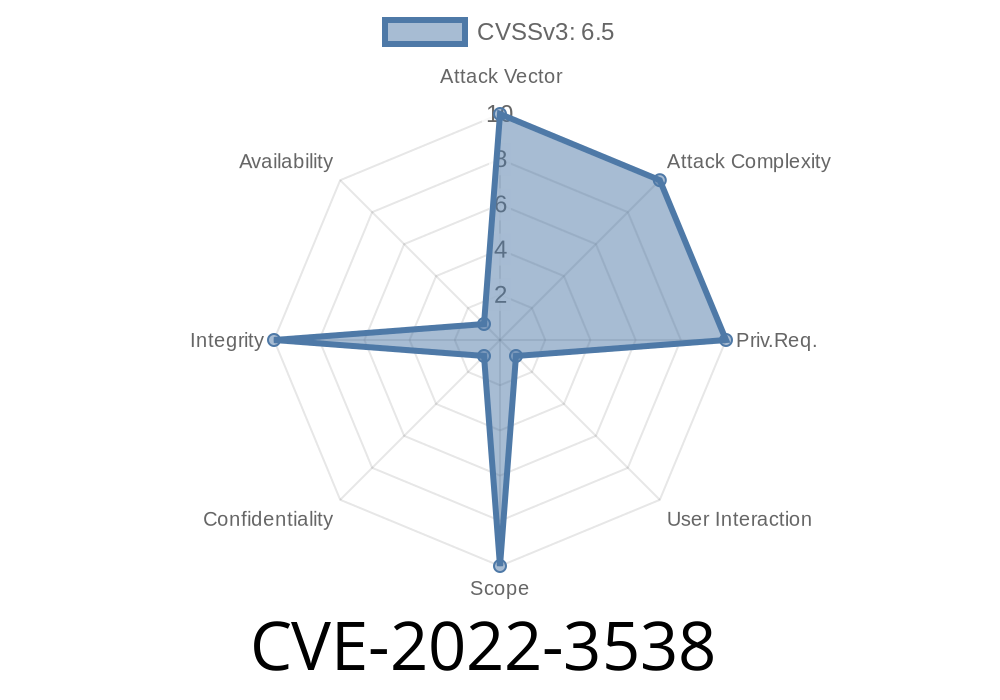
Wordpress CSRF Attack via Webmaster Tools
A security issue has been discovered in the WordPress Webmaster Tools, which allows an attacker to execute arbitrary code with admin permissions. The vulnerability allowed an attacker to trigger a cross-site request forgery (CSRF) attack through the Wordpress Webmaster Tools interface, and potentially allow an attacker to disable any plugins or themes on your site. This vulnerability was found by WordFence, who reported it to us via our public security issue tracker. All users of WordPress versions 4.7.1 and lower are recommended to upgrade immediately as this patch is already included in the latest version of WP Webmaster Tools. If you are running a version of Webmaster Tools Verification prior to 1.2, we strongly recommend updating as soon as possible as disabling plugin via the webmaster tools is a very common task that almost all site owners perform, so it’s important that you consider this issue when updating to 1.2
Summary
This security issue affects all WordPress sites running with the Webmaster Tools Verification plugin prior to 1.2. This includes the WordPress.com blogs, as well as any non-WordPress blog that uses this plugin. The vulnerability was discovered by WordFence, and we thank them for reporting it to us in our public security issue tracker.
Security issues are an unfortunate reality of any website and can lead to downtime and other negative consequences. Fortunately, there is a patch for this security issue that's already been released by WordPress.
Timeline
Published on: 11/14/2022 15:15:00 UTC
Last modified on: 11/16/2022 19:07:00 UTC