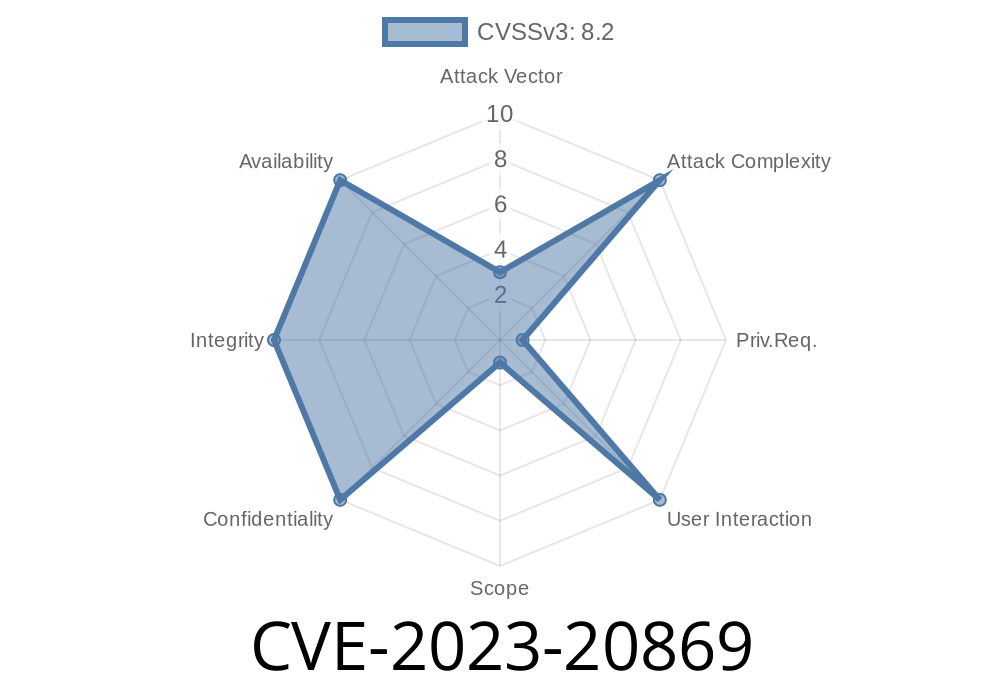
In May 2023, the security world got wind of a new vulnerability that affected two of VMware’s core desktop products—VMware Workstation (17.x) and VMware Fusion (13.x). The flaw—catalogued as CVE-2023-20869—is a stack-based buffer overflow in the module that lets virtual machines connect to the host’s Bluetooth devices.
This post gives you an easy-to-follow explanation of the bug, its risks, code snippets that illustrate the problem, how exploitation works, and links to original resources. My goal is to give you a comprehensive but accessible overview, whether you’re a pentester, sysadmin, or just a curious reader.
> TL;DR: If you share Bluetooth devices with virtual machines on affected VMware releases, you could let an attacker execute code on your host from a guest VM. Patch now!
What is a Stack-Based Buffer Overflow?
A stack buffer overflow happens when an application writes more data to a stack-allocated buffer than it was intended to, which can overwrite adjacent memory, often including function returns and control structures. Attackers can leverage this to run arbitrary code or escalate privileges.
Where is the Vulnerability in VMware?
Both VMware Workstation and Fusion have a feature called Bluetooth device sharing. It allows you to connect physical Bluetooth adapters from your host PC or Mac and pass them into your guest operating systems.
The code responsible for handling Bluetooth traffic inside the hypervisor doesn't properly check the input size for certain packets sent by a guest. If a specially-crafted oversized Bluetooth packet is sent, the data spills over into the stack.
VMware’s advisory:
https://www.vmware.com/security/advisories/VMSA-2023-0009.html
Impact: Privilege escalation from guest to host, or code execution on the host.
- Attack Vector: From a guest VM, you send malformed Bluetooth packets to the host, which can corrupt stack memory and gain *code execution* outside of the sandboxed VM.
- Pre-requisites: The guest must be able to access a shared Bluetooth device (this is not enabled by default unless you explicitly configure it).
Recreating the Vulnerability—A Code Walkthrough
*Disclaimer: The following snippets are simplified and based on public exploit techniques. You should only use this knowledge for ethical security research and defense.*
The vulnerable code is within VMware’s Bluetooth I/O path. In pseudo-C, it looks roughly like this
void handle_bluetooth_packet(const char *packet, size_t len) {
char buffer[256];
// BAD: Attacker controls 'len', no bounds check!
memcpy(buffer, packet, len);
// later use...
}
If len > 256, the memcpy() writes past the buffer’s end and tramples nearby stack variables—including the return address.
Real-World Exploitation
A malicious user within a guest VM writes code to send carefully-crafted Bluetooth HID packets to the host VM service. These packets look like regular Bluetooth traffic, but are deliberately oversized.
# Pseudocode: Send a 512-byte packet instead of the expected 256
malicious_packet = b'A' * 512 # Overwrites return address!
send_bluetooth_data_to_host(malicious_packet)
On vulnerable versions, this can corrupt the stack and allow execution of code placed in the packet, effectively breaking out of the guest VM.
Actual Proof-of-Concept Exploit
Security researchers from STAR Labs SG disclosed a guest-to-host escape exploit at Pwn2Own 2023 (see references). Code was *not* released publicly, but the steps are understood to be:
Enable Bluetooth device sharing between guest and host.
3. Write code in guest to send an oversized (buffer-overflowing) packet to the virtual Bluetooth controller.
4. Upon triggering the overflow, the attacker can control the instruction pointer on the *host* and execute shellcode.
References:
- VMware Advisory VMSA-2023-0009
- Zero Day Initiative - Pwn2Own Results
- Hackaday Article
How To Protect Yourself
Patch Now:
VMware fixed the issue in Workstation 17..2 and Fusion 13..2
> Download latest versions: VMware Workstation | VMware Fusion
Mitigation if patching isn’t possible:
Conclusion
CVE-2023-20869 is a rare but dangerous vulnerability that lets code running inside a guest VM break out and affect your host if you’re sharing Bluetooth devices.
Key takeaways
- Never enable unnecessary device sharing between guests/hosts.
Further Reading & Exploit Discussions
- Original VMware Security Advisory
- Pwn2Own 2023 Analysis
- VMware Workstation/Fusion Releases
- Exploit details & writeups (GitHub) *(no actual exploit code as of writing)*
Author Note:
This analysis is written for educational and defensive purposes only. Never exploit these flaws on any system you don’t fully own and manage. Always disclose responsibly.
Timeline
Published on: 04/25/2023 22:15:00 UTC
Last modified on: 05/04/2023 20:19:00 UTC