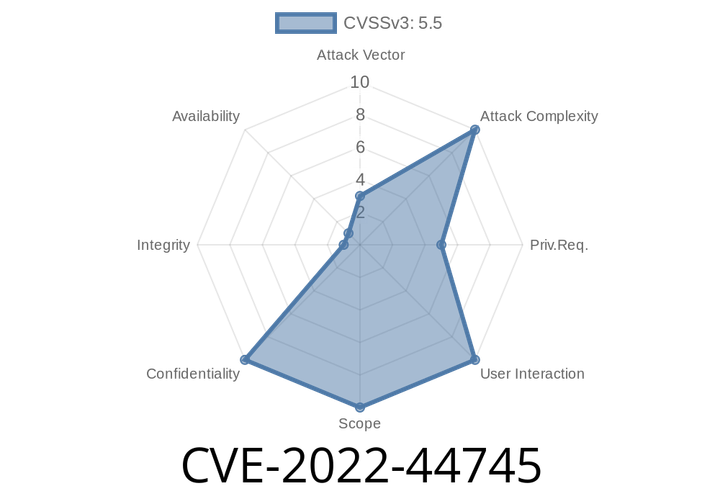
CVE-2022-44745 - Sensitive Information Leak Through Log Files in Acronis Cyber Protect Home Office (Windows)
In November 2022, a security vulnerability was disclosed under the identifier CVE-2022-44745, impacting earlier versions of Acronis Cyber Protect Home Office (formerly Acronis True Image)
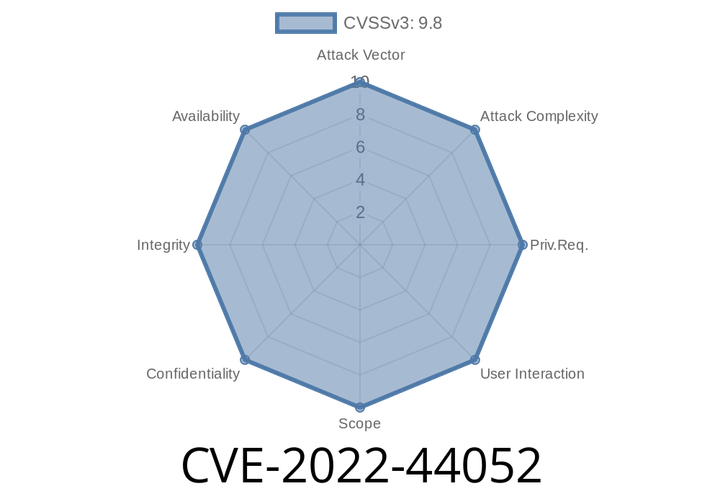
CVE-2022-44052 - Unpacking a Python Supply Chain Attack — Malicious Backdoor in d8s-dates and d8s-htm
Python’s rich package ecosystem is one of its biggest strengths, but it’s also a major attack surface. Recent supply chain incidents have shown
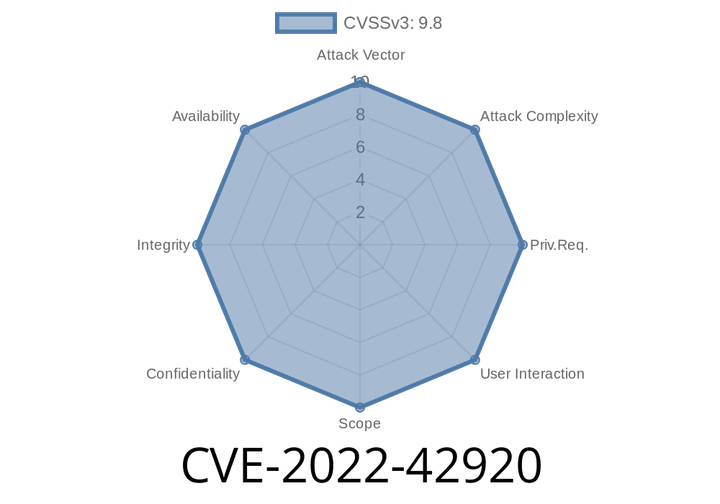
CVE-2022-42920 - Breaking Down the Apache Commons BCEL Bytecode Generation Vulnerability
In late 2022, a significant vulnerability—tracked as CVE-2022-42920—was uncovered in the popular Java library Apache Commons BCEL. This bug goes well beyond a
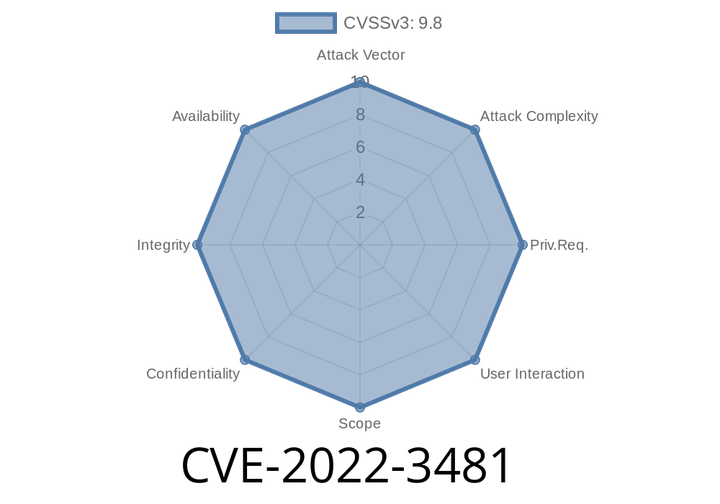
CVE-2022-3481 - Unauthenticated SQL Injection in WooCommerce Dropshipping Plugin (WordPress, < 4.4)
The world of WordPress plugins is vast, but sometimes even popular plugins contain severe security flaws. One such flaw—CVE-2022-3481—was discovered in the WooCommerce
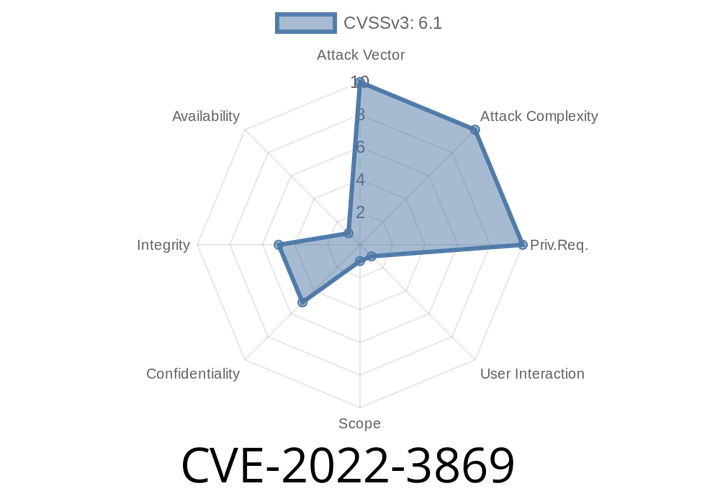
CVE-2022-3869 - Code Injection Vulnerability in Froxlor (GitHub) Prior to .10.38.2 – Explained With Exploit Example
When managing web hosting, many sysadmins turn to open-source panels like Froxlor for their flexibility and control. But open-source means open to both innovation and
Episode
00:00:00
00:00:00