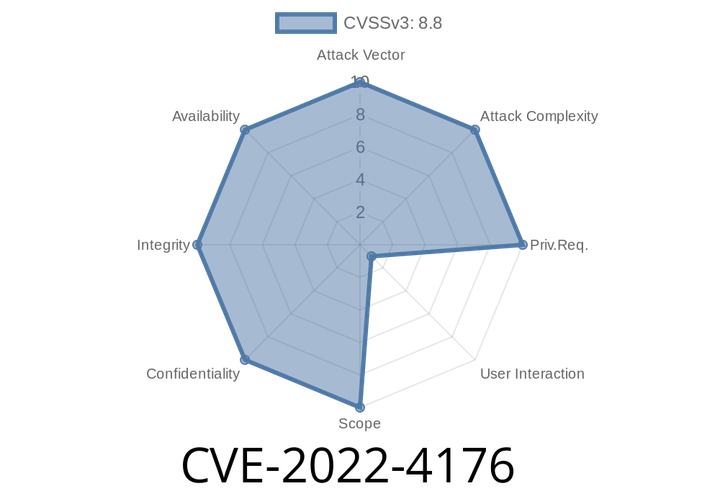
CVE-2022-4176 An out of bounds write in Lacros Graphics in Google Chrome on Chrome OS and Lacros prior to 108.0.5359.71 allowed a remote attacker to exploit heap corruption via UI interactions.
This issue was fixed in version 9.5.5.5. The issue existed due to a race condition where the out of bounds write could
CVE-2022-36962 - Remote Command Injection in SolarWinds Platform Explained
---
Introduction
In late 2022, a significant vulnerability was discovered in the SolarWinds Platform: CVE-2022-36962. This flaw openly allowed remote attackers with control over the
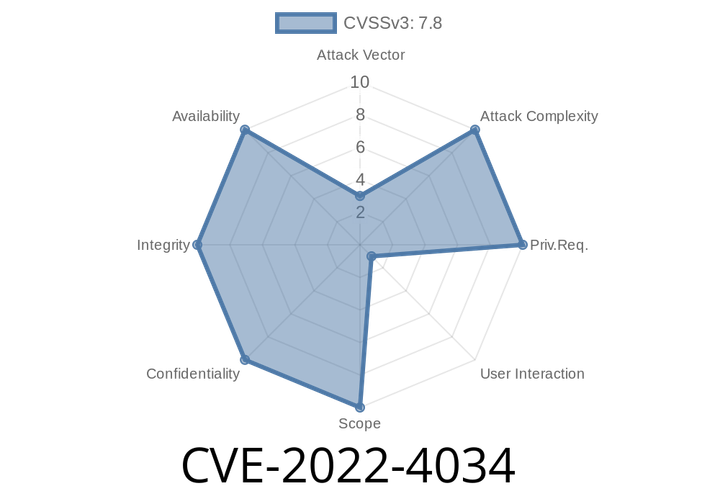
CVE-2022-4034 - CSV Injection in Appointment Hour Booking Plugin for WordPress (Up to v1.3.72) — Step-by-step Exploit Explained
If you run a WordPress site and rely on plugins to manage bookings, security must be a constant concern. A recently disclosed vulnerability, CVE-2022-4034, found
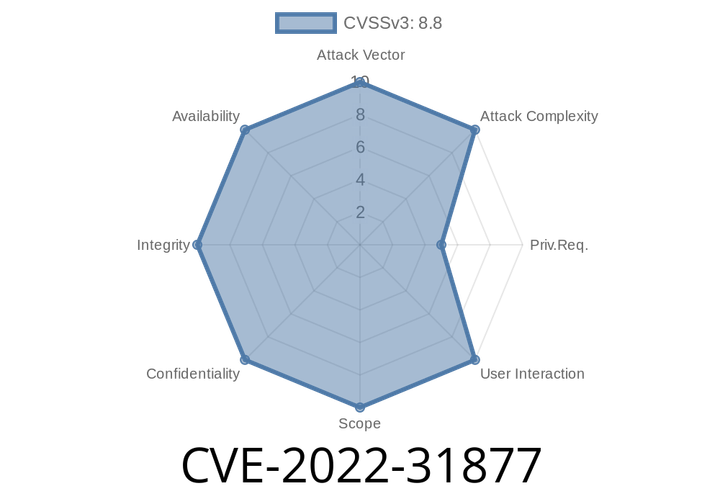
CVE-2022-31877 - Privilege Escalation in MSI Center's TerminalServer Explained
MSI, a popular hardware manufacturer, ships a software suite called “MSI Center” to help manage system settings, firmware, and more. In June 2022, cybersecurity researchers
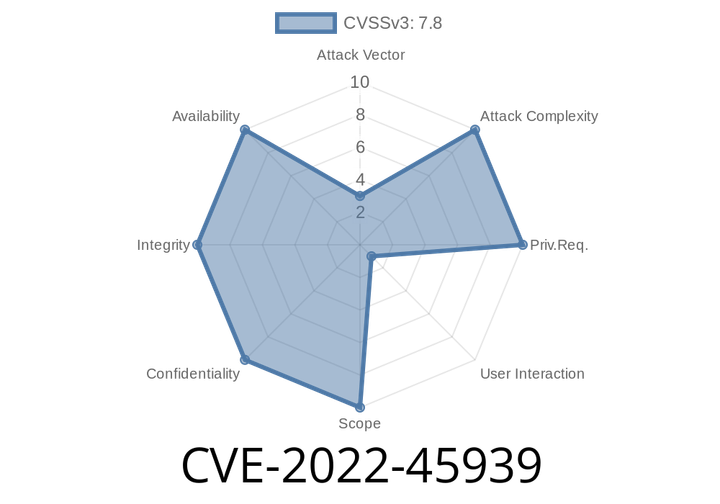
CVE-2022-45939 In GNU Emacs through 28.2, attackers can execute commands in the name of a source-code file because lib-src/etags.c uses the system C library function.
This may lead to ctags parsing arbitrary shell metacharacters to determine the location of the source code, potentially leading to code execution. lib-src/etags.c
Episode
00:00:00
00:00:00