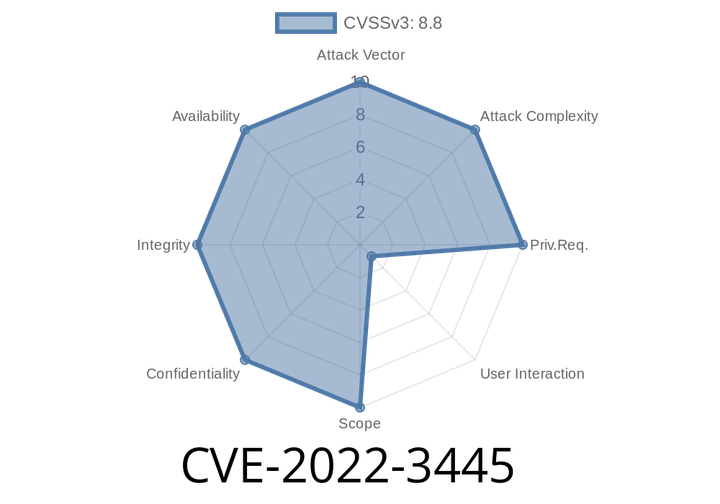
CVE-2022-3445 - Use-After-Free in Skia (Google Chrome) – Understanding the Bug, Its Exploitation, and How to Stay Safe
CVE-2022-3445 is a use-after-free vulnerability found in Skia, Google's open-source 2D graphics library used by Chrome. Before Chrome version 106..5249.119, a
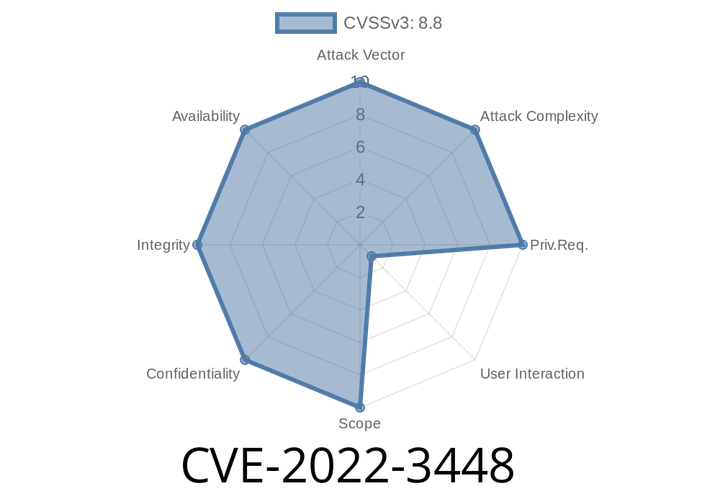
CVE-2022-3448 - Use-After-Free in Chrome Permissions API – Easy Explanation, Exploit Details, and Code Example
---
In October 2022, security researchers found a critical vulnerability in Google Chrome: CVE-2022-3448. If you’re curious about the risks, how it worked, and
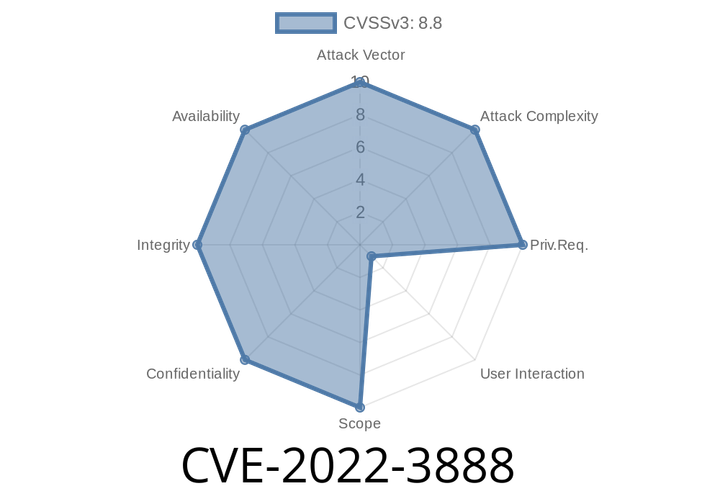
CVE-2022-3888 An attacker can exploit heap corruption in Google Chrome prior to 107.0.5304.106 to gain remote access.
Note that this issue was only fixed in the current Chromium version. Google Chrome prior to version 107.0.5304.106 had a use after
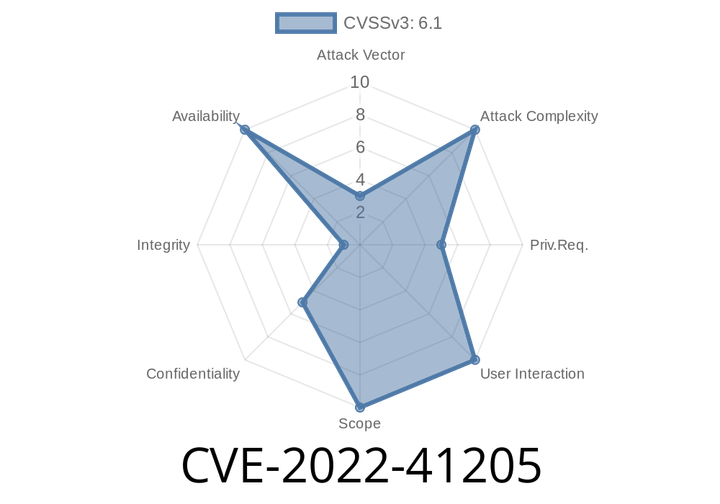
CVE-2022-41205 - SAP GUI Script Execution Vulnerability Explained (With PoC)
In September 2022, SAP fixed a critical vulnerability identified as CVE-2022-41205. This bug, found in the SAP GUI for Windows, allows a logged-in attacker to
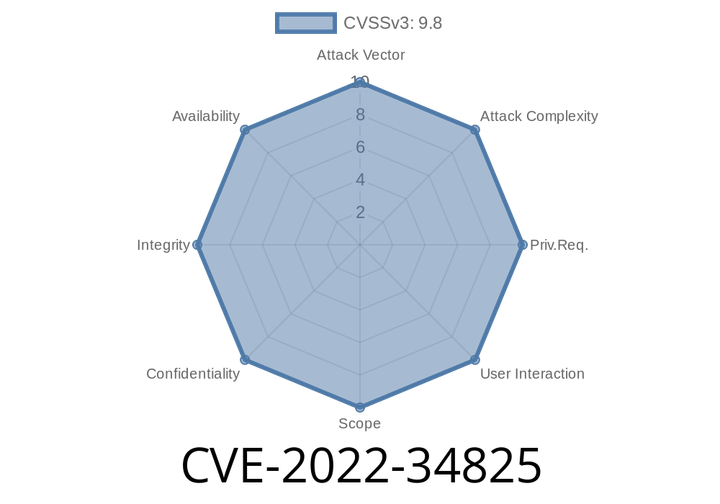
CVE-2022-34825 - Uncontrolled Search Path Element in CLUSTERPRO X and EXPRESSCLUSTER X for Windows Explained
In summer 2022, a critical vulnerability was disclosed with the identifier CVE-2022-34825. This flaw affected several disaster recovery and clustering products for Windows made by
Episode
00:00:00
00:00:00