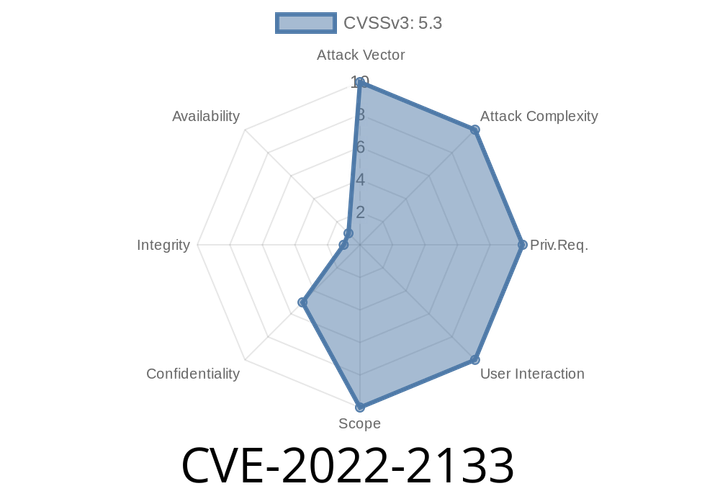
CVE-2022-2133 OAuth plugin before 6.22.6 doesn't validate token requests, which allows attackers to log into site with user's email address.
This access token can then be used to request any type of resource on the website that the user has access to. This could be
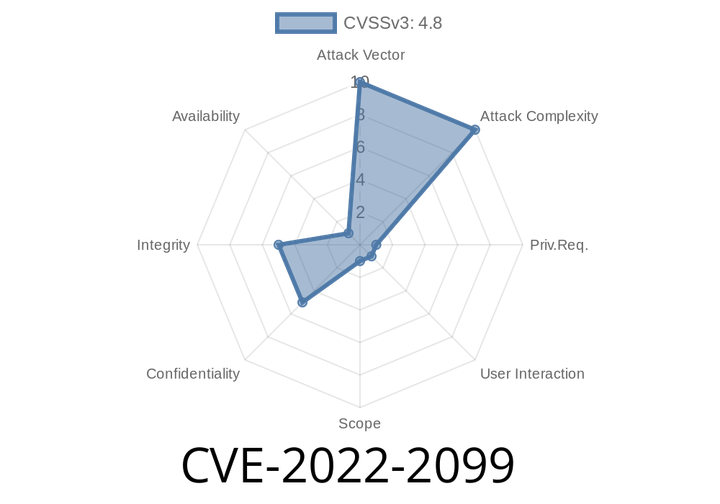
CVE-2022-2099 The WooCommerce WordPress plugin is vulnerable to stored HTML injection due to lack of escaping and sanitizing in the payment gateway titles.
The issue can lead to a variety of attacks like stealing credit card information, scamming customers, and other issues. In this update of the plugin,
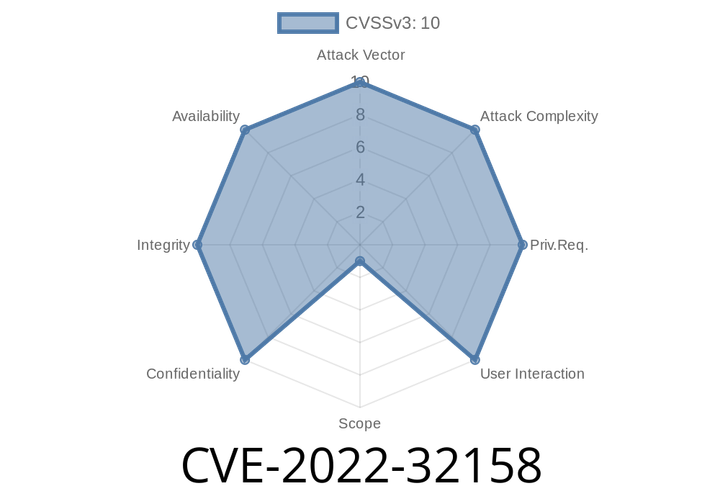
CVE-2022-32158 Deployment servers in versions 8.1.10.1, 8.2.6.1, and 9.0 allow clients to deploy forwarder bundles to each other.
This vulnerability was fixed in version 8.1.10.1, 8.2.6.1, and 9.0.
CVE-2022-32159
This vulnerability was fixed in version 8.
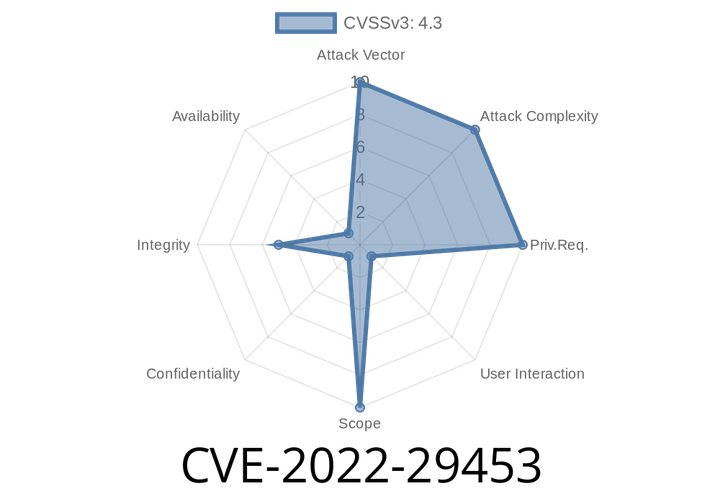
CVE-2022-29453 CSRF vulnerability in API key for Google Maps plugin = 1.2.1 at WordPress leading to key update.
This vulnerability can be exploited by hackers to change the settings of the target application or to steal data by exploiting the user’s trust
CVE-2022-29455 - DOM-based Reflected XSS in Elementor Website Builder Plugin (<= 3.5.5) — How It Works & Exploitation Details
Elementor is one of the world's most popular WordPress plugins, powering millions of websites with easy, drag-and-drop web design. However, serious vulnerabilities occasionally
Episode
00:00:00
00:00:00