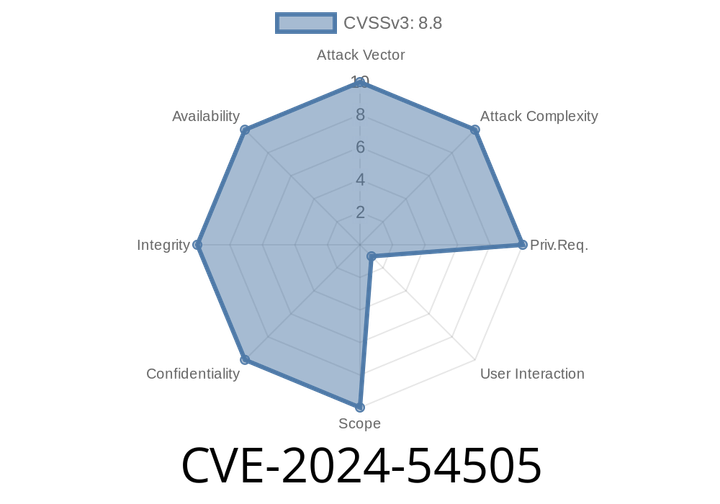
CVE-2024-54505 - Understanding Apple’s Memory Corruption Vulnerability and How It Was Fixed
Apple devices recently patched a serious security issue with CVE-2024-54505, a type confusion vulnerability that could allow attackers to corrupt memory by processing specially crafted
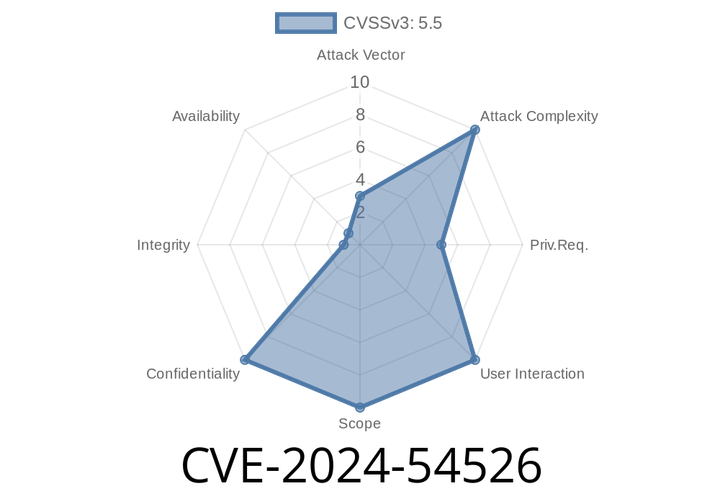
CVE-2024-54526 - Private Data Exposure in Apple Devices (Detailed Analysis and Exploit Example)
On June 2024, Apple patched a serious security vulnerability: CVE-2024-54526. This flaw could have let a malicious app read private information on Apple devices—impacting
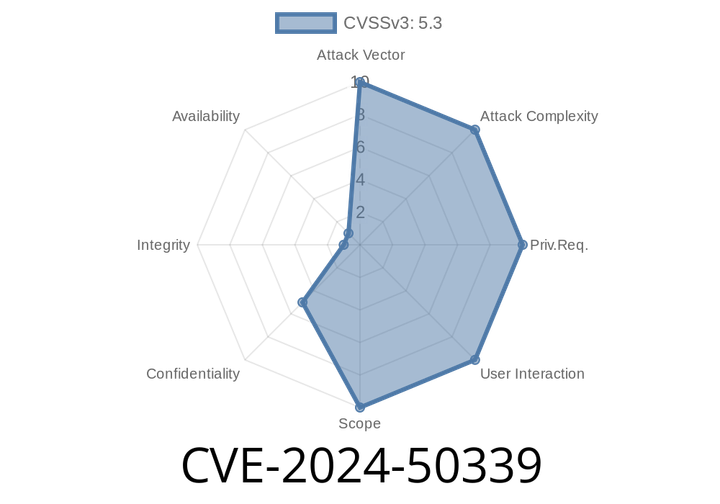
CVE-2024-50339 - How Attackers Can Hijack Any Session in GLPI Before Version 10..17
GLPI is an open-source IT asset management software popular among many organizations for tracking hardware, software, tickets, and much more. However, between versions 9.5.
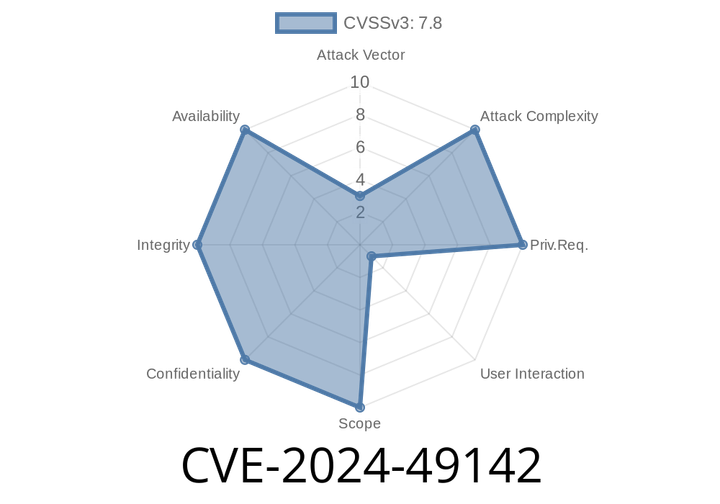
CVE-2024-49142 - Microsoft Access Remote Code Execution Vulnerability Explained
CVE-2024-49142 is a critical security vulnerability affecting Microsoft Access, the popular database management software included in Microsoft Office. This vulnerability allows a remote attacker to
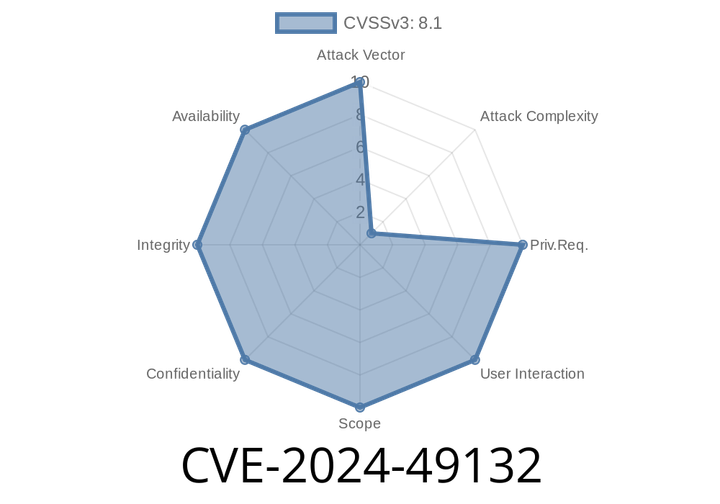
CVE-2024-49132 - Windows Remote Desktop Services Remote Code Execution Vulnerability Explained
In early June 2024, cybersecurity experts discovered a critical vulnerability in Microsoft’s Remote Desktop Services (RDS) identified as CVE-2024-49132. This flaw enables remote attackers
Episode
00:00:00
00:00:00