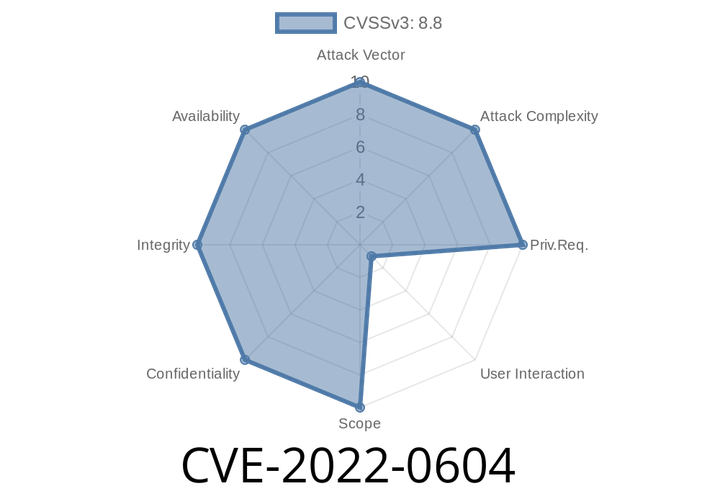
CVE-2022-0604 An attacker who convinced a user to install a malicious extension could exploit a heap buffer overflow via a crafted HTML page.
An attacker could also potentially exploit these issues by convincing a user to install a malicious extension.
CVE-2018-6025 Chrome on Android before the 2018Q3 release,
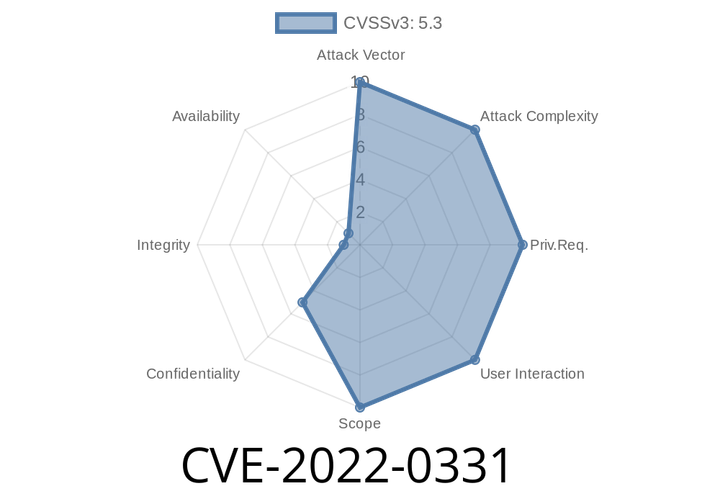
CVE-2022-0331 Webadmin leaks serial numbers of vulnerable Sophos Firewalls. An attacker can use this to impersonate the affected device.
The device serial number is used to identify a specific device. For instance, it can be used to determine if a device is a new
CVE-2022-22611 - Out-of-Bounds Read in Apple Image Processing Explained (With Exploit Details)
Security vulnerabilities in major Apple products always get people’s attention, and CVE-2022-22611 is no exception. This bug could let an attacker run code on
CVE-2022-22640 - How a Memory Corruption Bug in Apple Devices Let Hackers Execute Code as Kernel
In early 2022, Apple patched a severe security flaw labeled CVE-2022-22640. This vulnerability let malicious apps gain kernel-level privileges by exploiting a memory corruption issue.
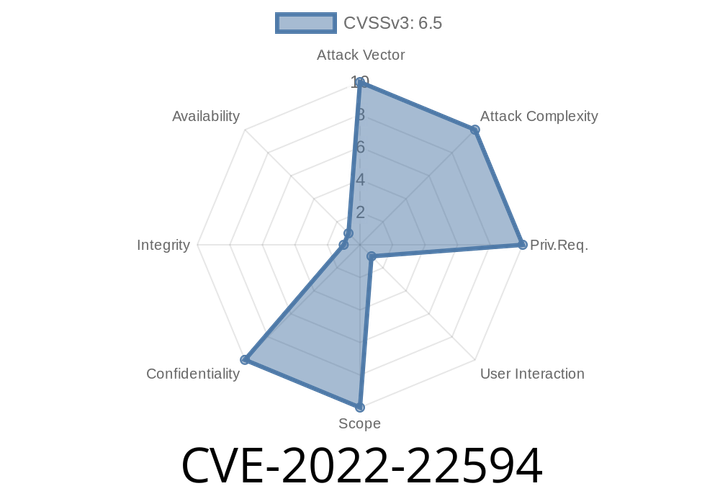
CVE-2022-22594 - Cross-Origin IndexedDB Vulnerability Leaks Sensitive User Data on Apple Devices
In January 2022, Apple patched a major privacy vulnerability: CVE-2022-22594. This bug exposed how IndexedDB—the main browser database for websites—could cross the boundaries
Episode
00:00:00
00:00:00