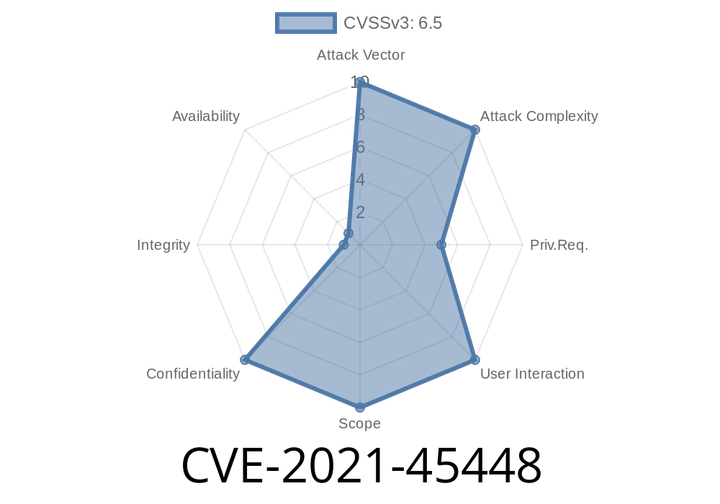
CVE-2021-45448 - How Directory Traversal in Pentaho Business Analytics Server Exposes Sensitive Data
CVE-2021-45448 significantly impacts older versions of Pentaho Business Analytics Server, specifically those before 9.2..2 and 8.3..25. Through a flaw in the
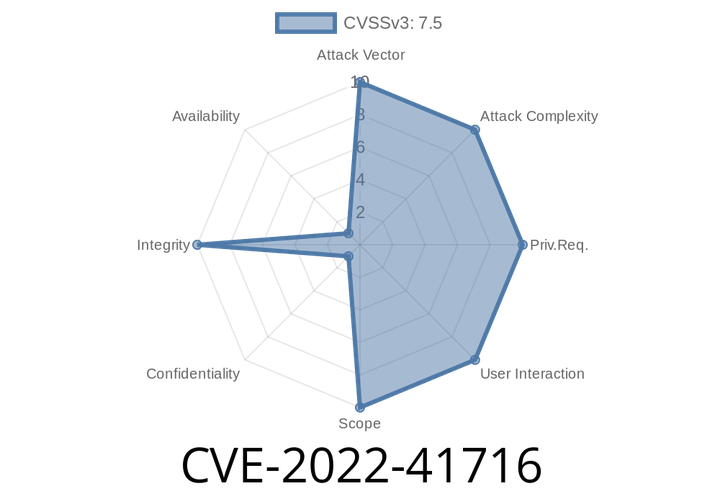
CVE-2022-41716 - Exploiting Unsanitized NUL Values to Set Arbitrary Environment Variables on Windows
In late 2022, a security vulnerability was discovered in Go (Golang) that affects how environment variables are handled on the Windows platform. This critical flaw,
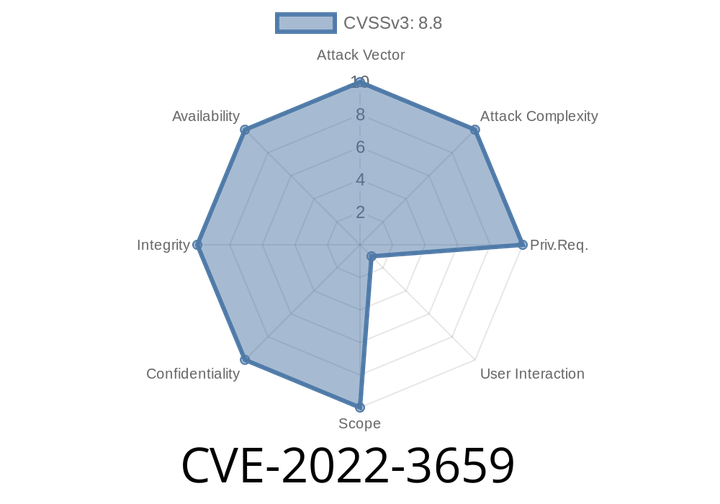
CVE-2022-3659 An attacker who convinces a user to perform specific UI interactions could exploit heap corruption to get remote access.
This issue was addressed by introducing a delay before UI interactions are enabled to prevent immediate exploitation.
In Google Chrome on Windows, input events are
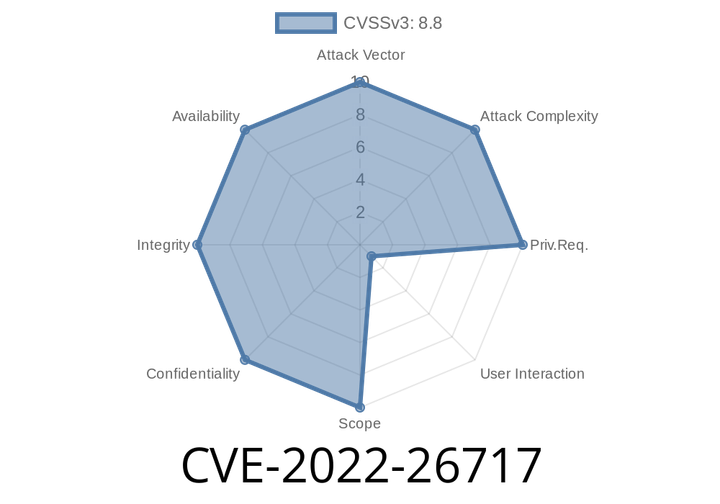
CVE-2022-26717 - Apple WebKit "Use After Free" Vulnerability Explained – How It Was Exploited and Fixed
In 2022, security researchers uncovered CVE-2022-26717, a dangerous "use after free" vulnerability in Apple's WebKit, the browser engine that powers Safari
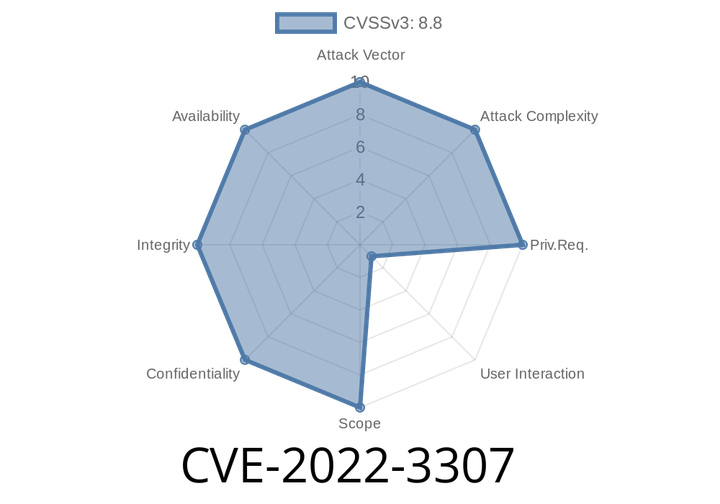
CVE-2022-3307 An attacker can exploit heap corruption in Google Chrome before version 106.0.5249.62 if a malicious page is used.
After fixing this issue in the stable channel, we encourage users to update to the latest version, which will be 106.0.5249.62. A
Episode
00:00:00
00:00:00