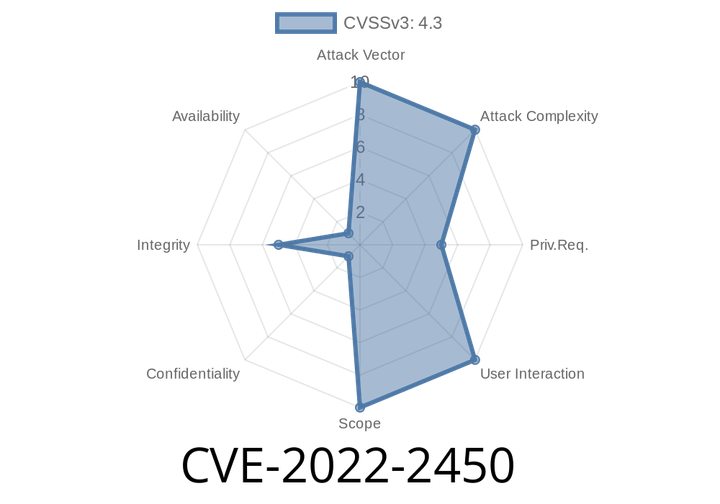
CVE-2022-2450 The reSmush.it: the only free Image Optimizer & compress plugin before 0.4.4 lacks authorization, which allows subscribers to call it.
Even though reSmush.it has an “Authorization” setting, it has no enforcement method, meaning that anyone with the ability to set this option can use
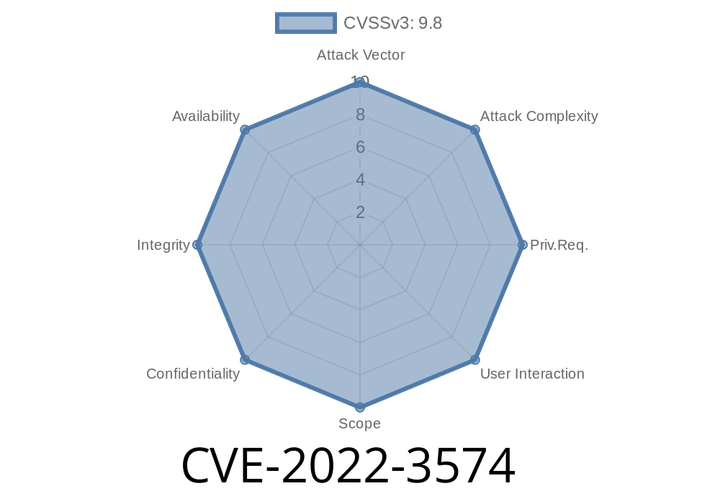
CVE-2022-3574 The WPForms Pro plugin before 1.7.7 does not validate form data when exporting, which could lead to CSV injection.
If a site administrator saved the generated CSV on a local hard drive and then transferred it to a different site via a file transfer,
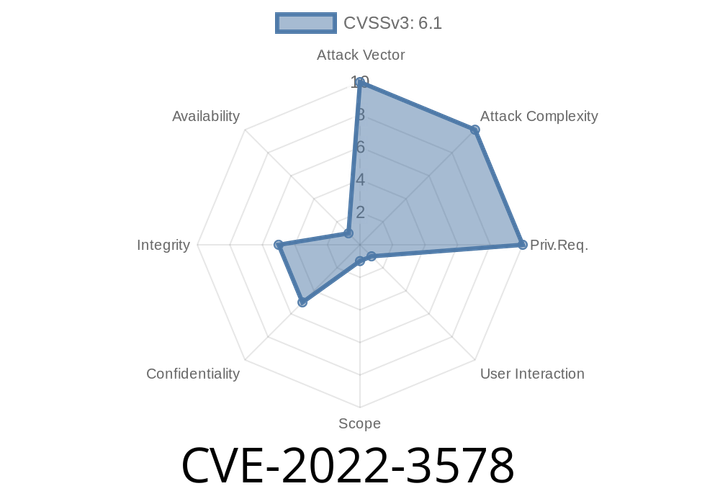
CVE-2022-3578 The ProfileGrid WordPress plugin before 5.1.1 is vulnerable to Reflected XSS, which could be used to steal cookies and other data.
attack where a malicious user could inject malicious script code into the website via the website’s input parameters. If you are using this plugin
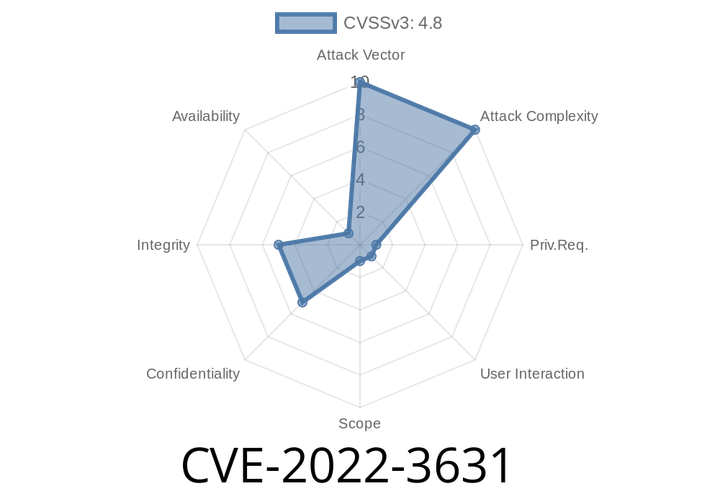
CVE-2022-3631 The OAuth plugin through 1.1.0 doesn't sanitize and escape some of its settings, which could allow high-privilege users to perform Stored Cross-Site Scripting attacks.
The high-privilege user could create a malicious link that would be parsed and executed by the web server if the unfiltered_html setting is disabled.
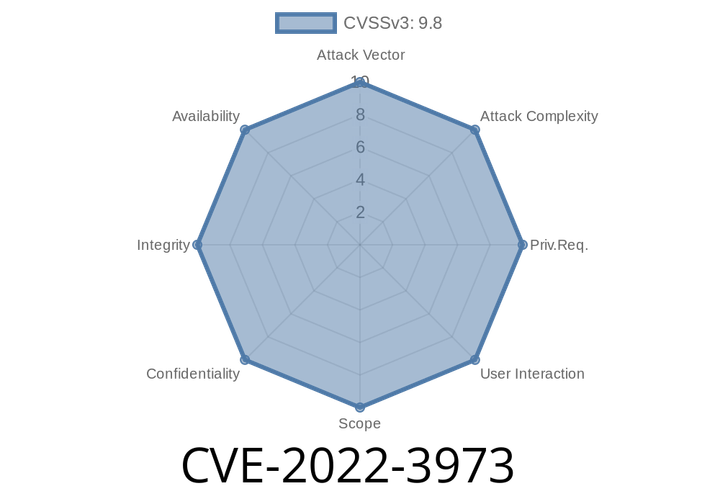
CVE-2022-3973 A critical vulnerability has been found in Pingkon HMS-PHP Data Pump Metadata. The manipulation of the argument uname/pass leads to sql injection.
The researcher of the problem discovered by the RedTeam Pentesting security group states that the injectable sql code is as follows: Injectable sql code: [Select]
Episode
00:00:00
00:00:00