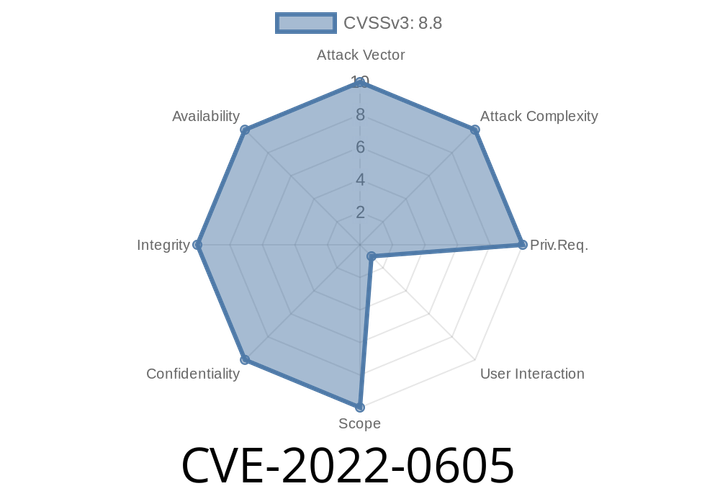
CVE-2022-0605 The API in Google Chrome allowed an attacker to exploit heap corruption after an extension is installed and a user is convinced to interact.
An attacker could trick a user to install a malicious extension and convince a user to interact with the page such as clicking on a
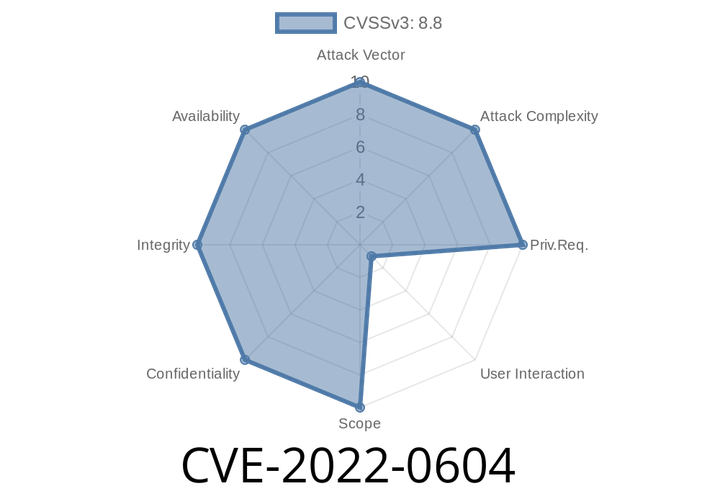
CVE-2022-0604 An attacker who convinced a user to install a malicious extension could exploit a heap buffer overflow via a crafted HTML page.
An attacker could also potentially exploit these issues by convincing a user to install a malicious extension.
CVE-2018-6025 Chrome on Android before the 2018Q3 release,
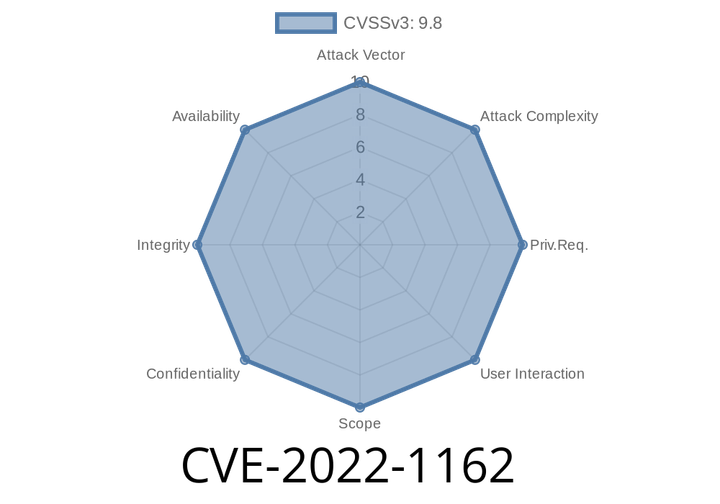
CVE-2022-1162 A hardcoded password was set for accounts registered using an OmniAuth provider (e.g
allowing attackers to potentially take over accounts A hardcoded password was set for SSH keys in GitLab EE/CE versions prior to 14.7.7,
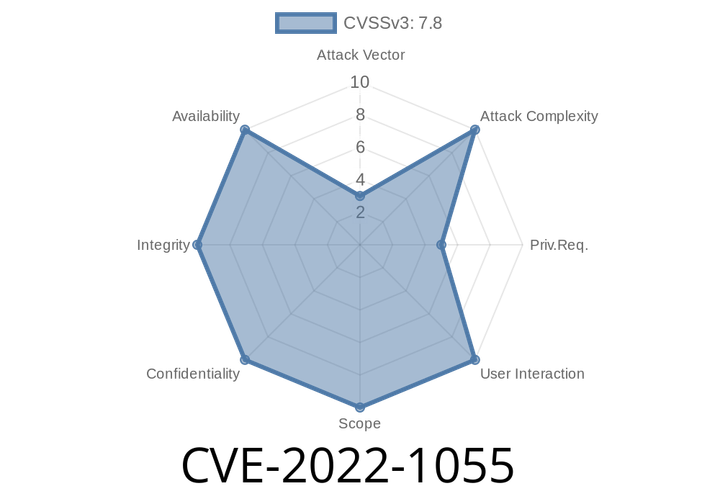
CVE-2022-1055 An use-after-free vulnerability exists in the tc_new_tfilter kernel component that could allow a local attacker to gain privilege escalation. The exploit requires unprivileged user namespaces.
Or running a non-vulnerable kernel version. An attacker can trick a user into visiting a malicious webpage by sending him/her a link or an
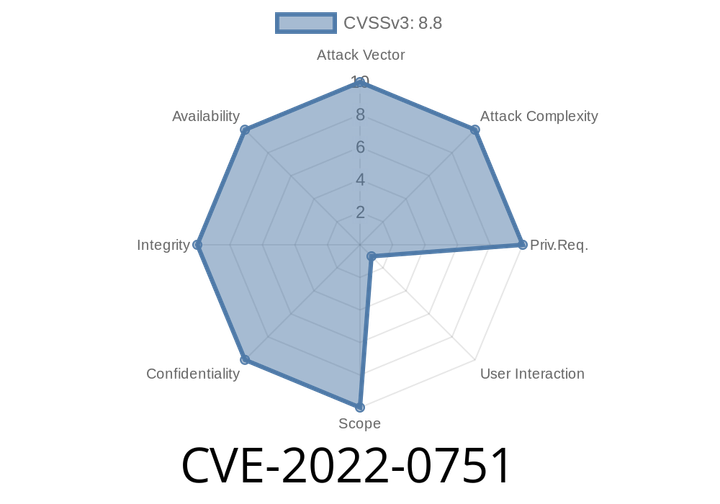
CVE-2022-0751 An attacker can create Snippets with misleading content which could trick unsuspecting users into executing arbitrary commands.
Snippet files are small text files which allow users to define custom commands to be executed in their project. If malformed, these files can contain
Episode
00:00:00
00:00:00